In case you’re looking for a variety of IRC client implementations, or always wondered how botnets and other malware looks on the inside, [maestron] has just the right thing for you. After years of searching and gathering the source code of hundreds of real-world botnets, he’s now published them on GitHub.
With C++ being the dominant language in the collection, you will also find sources in C, PHP, BASIC, Pascal, the occasional assembler, and even Java. And if you want to consider the psychological aspect of it, who knows, seeing their malicious creations in their rawest form might even give you a glimpse into the mind of their authors.
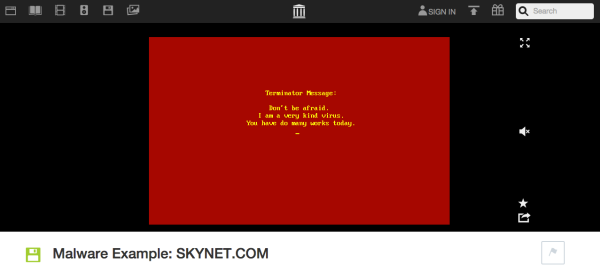
These sources are of course for educational purposes only, and it should go without saying that you probably wouldn’t want to experiment with them outside a controlled environment. But in case you do take a closer look at them and are someone who generally likes to get things in order, [maestron] is actually looking for ideas how to properly sort and organize the collection. And if you’re more into old school viruses, and want to see them run in a safe environment, there’s always the malware museum.