All things considered, it was a very bad week for aviation here in the United States. Three separate crashes, two of which involved US military aircraft, have left over 70 people dead. We’ll spare you the details since there are plenty of other places to get news like that, but we did want to touch on one bright spot in this week’s aviation news: the first successful supersonic flight by a US-made civilian aircraft. There are a lot of caveats to that claim, but it’s clear that Boom Supersonic is on a path to commercializing supersonic air transportation for the first time since the Concorde was retired. Their XB-1 “Baby Boom” test aircraft managed three separate supersonic runs during the January 28 test flight over the Mojave test range. As usual, Scott Manley has excellent coverage of the test flight, including a look at how Boom used a Starlink terminal and an iPhone to stream cockpit video.
super mario12 Articles
Super Mario Original Sound Tracks Get High Quality Remaster Thanks To Gigaleak
2020 saw many gigabytes of internal Nintendo data leaked on the broader internet. Known as the “Gigaleak”, it contained source codes and assets from many games. Using data from this leak, a group of enthusiasts has put together high-quality renditions of the SNES Super Mario World Original Sound Tracks (OST).
The work was made possible when source code from the Gameboy Advance remake of Super Mario World was found in the leaked data. The source code included the names of the samples, which were the same as were used in the original SNES game. This allowed the team to find the original samples amongst the gigabytes of leaked files.
We wondered what would be done with all that code, speculating that it would be a poison pill for the emulator scene. This type of hack wasn’t even on our radar and we’re delighted to see the project come to light. The reproduced songs have an altogether different quality than the original SNES soundtrack. This is largely due to the samples not having to be compressed or cut down to fit on a cartridge and work with the console’s sound chip. Other variances in the sound also come from the fact that unlike in the game, the samples in these renditions don’t match the play lengths in the original game.
Regardless of the changes, it’s interesting to hear a more full, rounded sound of these classic video game tunes. It reminds us somewhat of the later CD console era, when sound designers were able to break free of the limitations of earlier hardware. Of course, we still bow at the alter of chiptune, though — and this MIDI Gameboy mod is a great place to start if you’re curious. Video after the break.
Continue reading “Super Mario Original Sound Tracks Get High Quality Remaster Thanks To Gigaleak”
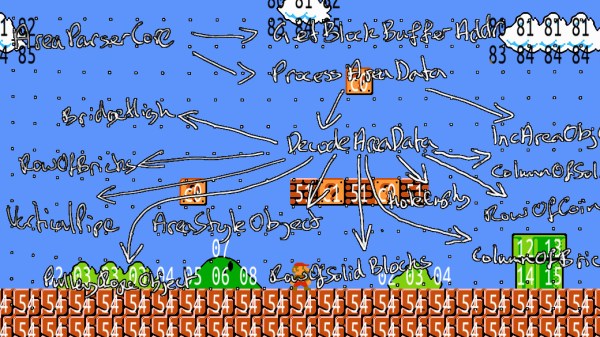
Find Your Level – Extracting NES Game Data Using Python
Just this summer, the Nintendo Entertainment System had its 35th release anniversary, and even after years of discontinuation, it is still going strong in the hacker community. Exhibit A: [Matthew Earl]. For one of his upcoming projects, [Matthew] needed to get his hands on the background images of the NES classic Super Mario Bros. Instead of just getting some ready-rendered images and stitching them together, he decided to take care of the rendering himself, once he extracts the raw game data.
Since there is no official source code available for Super Mario Bros, [Matthew] used a disassembled version to get started looking for the image data. To avoid reading through thousands of lines of assembly code, and to also see what actually happens during execution, he wrapped the game’s ROM data into py65emu, a Python library emulating the 6502, the CPU that drives the NES. By adding a simple wrapper around the emulator’s memory handler that tracks reads on uninitialized data, [Matthew] managed to find out which parameters he needs to feed to the parser routine in order to get the image tile data. After an excursion into the Picture Processing Unit (PPU) and its memory arrangements, [Matthew] had everything he needed to create the Python script that will render the game background straight from its ROM data.
Even if extracting NES game data is not your thing, the emulator concept [Matthew] uses might be still worth a read. On the other hand, if you want to dig deeper into the NES, you should definitely have a look at emulating an SNES game on a NES, presented on the NES itself.
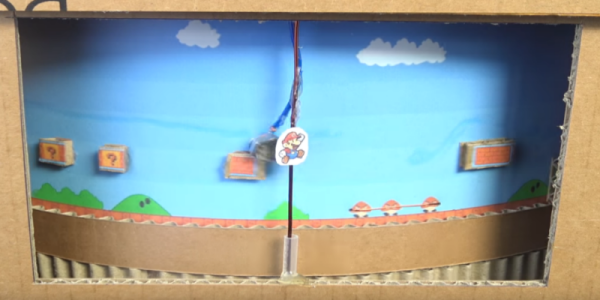
Super Low Tech Mario
Browsing around the depths of the Internet we came across a super low tech version of Super Mario from [Sata Productions]. The video presents a complete tutorial on how to make a playable, cardboard version of the famous Super Mario game. If you are a fan, you probably going to like this.
You basically need cardboard, a hot glue gun, a ball bearing, a couple of DC motors, some iron BBs, some magnets, batteries, some wires… it sounds just like shopping list for a MacGuyver episode. But it works and it’s playable. It has a wired remote control, you control Mario to move and make him jump up and down in a kind of turning dashboard game. It even has a game over screen when Mario dies. Yes, Mario can die in this cardboard version. If you want to make a custom version you can always print a bigger level and resize the cardboard box.
Super Mario has had its shares of hacks, like this interface hack using a Kinect to control Mario or this super tricky jailbreak hack that allows players to run their own game mods, but this one is just on another level: a low tech approach. It seems like it could be a fun weekend project, especially if you have kids. If you’re not into Super Mario, it’s possible to just print a different game, the supporting platform is pretty generic and could support several simplified platform games.
Check out the video:
Arbitrary Code Execution Is In Another Castle!
When one buys a computer, it should be expected that the owner can run any code on it that they want. Often this isn’t the case, though, as most modern devices are sold with locked bootloaders or worse. Older technology is a little bit easier to handle, however, but arbitrary code execution on something like an original Nintendo still involves quite a lot of legwork, as [Retro Game Mechanics Explained] shows with the inner workings of Super Mario Brothers 3.
While this hack doesn’t permanently modify the Nintendo itself, it does allow for arbitrary code execution within the game, which is used mostly by speedrunners to get to the end credits scene as fast as possible. To do this, values are written to memory by carefully manipulating on-screen objects. Once the correct values are entered, a glitch in the game involving a pipe is exploited to execute the manipulated memory as an instruction. The instruction planted is most often used to load the Princess’s chamber and complete the game, with the current record hovering around the three-minute mark.
If you feel like you’ve seen something like this before, you are likely thinking of the Super Mario World exploit for the SNES that allows for the same style of arbitrary code execution. The Mario 3 hack, however, is simpler to execute. It’s also worth checking out the video below, because [Retro Game Mechanics Explained] goes into great depth about which values are written to memory, how they are executed as an instruction, and all of the other inner workings of the game that allows for an exploit of this level.
Continue reading “Arbitrary Code Execution Is In Another Castle!”
Super Mario Run(s) — Away With Your Money
If you are an Android user and a big fan of Super Mario beware: there is no Android version! There has been no official news on the Android version yet, let alone a version of the game. There is, however, a version circulating outside of Google Play market that will steal your bank account.
Right now attackers are taking advantage of the game’s popularity and Android users despair to spread malware posing as an Android version of Super Mario Run as they did in the past for Pokemon GO. The trojan is called Android Marcher and has been around since 2013, mostly targeting mobile users financial information. After installation, the application attempts to trick users with fake finance apps and a credit card page in an effort to capture banking details. The malware also locks out Google Play until the user supplies their credit card information.
In this new variant of Marcher, it can monitor the device and steal login data of regular apps, not just banking and payment apps, and send the stolen data back to command and control (C&C) servers. Facebook, WhatsApp, Skype, Gmail, the Google Play store are all vulnerable. Criminals can exploit these stolen accounts to carry out additional fraud.
Zscaler researchers advice is:
To avoid becoming a victim of such malware, it is a good practice to download apps only from trusted app stores such as Google Play. This practice can be enforced by unchecking the “Unknown Sources” option under the “Security” settings of your device.
We may add to turn on “App Verification”. Verify Apps regularly checks activity on your device and prevents or warns you about potential harm. Verify Apps is on by default, as is Unknown Sources turned off. Verify Apps also checks apps when you install them from sources other than Google Play. Of course, there is a privacy trade-off. Some information has to be sent about the apps you install back to Google.
The main advice is: use common sense. It’s common practice for companies to release official apps versions through Google Play and highly unlikely to do it via any other way.
Thwomp Drops Brick On Retro Gaming
[Geeksmithing] wanted to respond to a challenge to build a USB hub using cement. Being a fan of Mario Brothers, a fitting homage is to build a retro-gaming console from cement to look just like your favorite Mario-crushing foe. With a Raspberry Pi Zero and a USB hub embedded in it, [Geeksmithing] brought the Mario universe character that’s a large cement block — the Thwomp — to life.
[Geeksmithing] went through five iterations before he arrived at one that worked properly. Initially, he tried using a 3D printed mold; the cement stuck to the plastic ruining the cement on the face. He then switched to using a mold in liquid rubber (after printing out a positive model of the Thwomp to use when creating the mold). But the foam board frame for the mold didn’t hold, so [Geeksmithing] added some wood to stabilize things. Unfortunately, the rubber stuck to both the foam board and the 3D model making it extremely difficult to get the model out.
![Like [Han] in carbonite, that's a Rapsberry Pi Zero being encased in cement](https://hackaday.com/wp-content/uploads/2016/12/raspberry-pi-thwomp.png?w=400)
The final casting worked and after painting, [Geeksmithing] had a finished cement Thwomp console that would play retro games. He missed the deadline for the USB Hub Challenge, but it’s still a great looking console, and his video has a lot of detail about what went wrong (and right) during his builds. There’s a great playlist on YouTube of the other entries in the challenge, check them out along with [Geeksmithing]’s video below!