Even in the early days of the Cold War, it quickly became apparent that simply having hundreds or even thousands of nuclear weapons would never be a sufficient deterrent to atomic attack. For nuclear weapons to be anything other than expensive ornaments, they have to be part of an engineered system that guarantees that they’ll work when they’re called upon to do so, and only then. And more importantly, your adversaries need to know that you’ve made every effort to make sure they go boom, and that they can’t interfere with that process.
In practical terms, nuclear deterrence is all about redundancy. There can be no single point of failure anywhere along the nuclear chain of command, and every system has to have a backup with multiple backups. That’s true inside every component of the system, from the warheads that form the sharp point of the spear to the systems that control and command those weapons, and especially in the systems that relay the orders that will send the missiles and bombers on their way.
When the fateful decision to push the button is made, Cold War planners had to ensure that the message got through. Even though they had a continent-wide system of radios and telephone lines that stitched together every missile launch facility and bomber base at their disposal, planners knew how fragile all that infrastructure could be, especially during a nuclear exchange. When the message absolutely, positively has to get through, you need a way to get above all that destruction, and so they came up with the Emergency Rocket Communication System, or ERCS.
Continue reading “Radio Apocalypse: America’s Doomsday Rocket Radios”





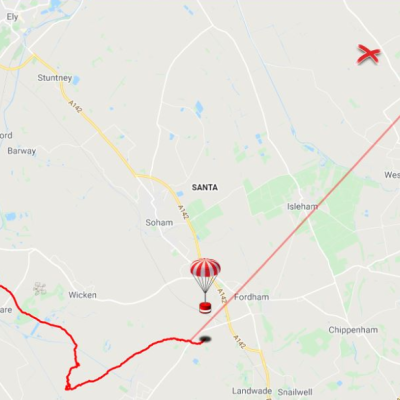

 The payload container is a hollow tube with a 3D printed threaded adaptor attached to one end. Payload goes into the tube, and the tube inserts into a hole in the bulkhead, screwing down securely. The result is an easy way to send up something like a GPS tracker, possibly with a LoRa module attached to it. That combination is a popular one with high-altitude balloons, which, like rockets, also require people to retrieve them after not-entirely-predictable landings. LoRa wireless communications have very long range, but that doesn’t help if there’s an obstruction like a hill between you and the transmitter. In those cases,
The payload container is a hollow tube with a 3D printed threaded adaptor attached to one end. Payload goes into the tube, and the tube inserts into a hole in the bulkhead, screwing down securely. The result is an easy way to send up something like a GPS tracker, possibly with a LoRa module attached to it. That combination is a popular one with high-altitude balloons, which, like rockets, also require people to retrieve them after not-entirely-predictable landings. LoRa wireless communications have very long range, but that doesn’t help if there’s an obstruction like a hill between you and the transmitter. In those cases,