The Bay Area Maker Faire starts today, but the Hackaday crew rolled in early for something new this year. Friday has traditionally been just for exhibitor setup but this year a few extra groups were on site to see everything come together. Most notably, school field trips. How awesome is it to skip the normal class schedule and hang out at the fair? Also able to get in are media and industry.
I had a great time. Watching everything get setup is often more interesting that seeing the finished display. It’s also much quieter, many fewer bodies (Saturday afternoon is usually a mad press of people) and people haven’t yet lost their voices or the fallen into the monotony of voicing the same explanation over and over again.
Above you can see a few of the friends I ran into. [Windell Oskay] is one of the 2015 Hackaday Prize Judges. He had a freshly minted copy of his new book which I first heard about when visiting Evil Mad Scientist Labs last fall. I also ran into [Kevin] who is the creator of the Arduboy. I first met him at BAMF last year and this year he makes a triumphant return with the new version of Arduboy which overshot it’s Kickstarter by an order of magnitude in just a few days. And who else should I bump into but [Brian Benchoff]. He lives in Pennsylvania and I in Wisconsin so we look forward to hanging out when Hackaday hits the road. I also said a quick hello to [Caleb Kraft] who was slinging veggie paella all evening.
[Brian], [Sophi], [Matt], [Jasmine], [Rich], and I will all be at tonight’s Hackaday Meetup. Anyone in the area won’t want to miss this one. There are a ton of awesome hackers already planning to clink glasses starting at 7pm. All you need to do to join in is RSVP.

The LEGO GP, get it?

An amazing world of masking tape

Probability machine

Google Wing — autonomous package delivery

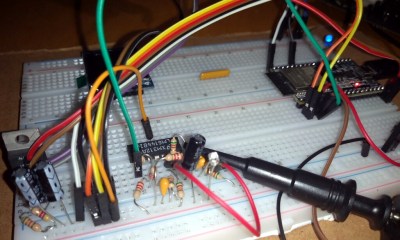
The guts of Ark Reactor which grows probiotics
Back to the action; I made a quick Friday first pass which still took about three hours. The setup changes just a bit each year… generally things are in the same places but of course returning exhibitors have made a year of upgrades and there’s always a lot of fresh and new on hand. I don’t remember seeing the probability machine last year. It has reservoir of marbles at the top which are being steadily dropped into the “Plinko” style peg-board showing a distribution which has a higher probability toward the center.

Aquaponics grows food, filters water, and reuses fish waste as fertalizer

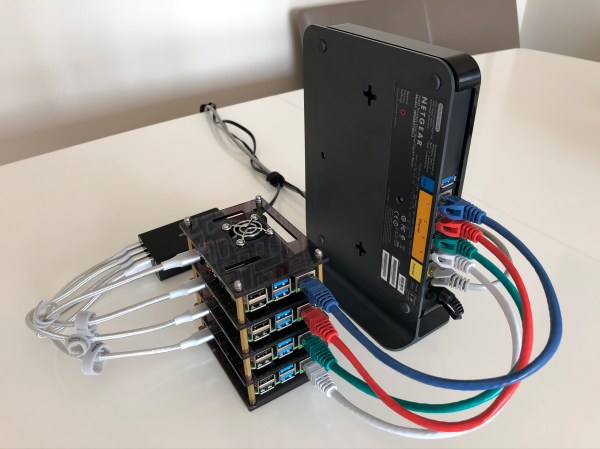
The business end of Firepick Delta

A huge sand plotter

SmartMatrix showing its colors

Lockpicking tent
Here are just a few more favorites. The Kijani Grows booth has a couple of full aquaponics setups that are worth checking out. I spent some time with the Firepick Delta guys. Sand plotters are always fun and there’s a giant one in one of the booths. I may try my hand at lock picking in The OPen Organization of Lockpickers tent today. And [Louis] of SmartMatrix is launching his Kickstarter to bring fully-assembled versions to people who don’t want to solder the one available in our store.
That’s all for now, I’m off to see as much as is humanly possible. If you’re at the Faire today or tomorrow track us down for some stickers and other swag, and don’t forget tonight’s meetup that I mentioned above!