It’s been quite a week for asteroid 2024 YR4, which looked like it was going to live up to its “city killer” moniker only to be demoted to a fraction of a percent risk of hitting us when it swings by our neighborhood in 2032. After being discovered at the end of 2024, the 55-meter space rock first popped up on the (figurative) radar a few weeks back as a potential risk to our home planet, with estimates of a direct strike steadily increasing as more data was gathered by professional and amateur astronomers alike. The James Webb Space Telescope even got in on the action, with four precious hours of “director’s discretionary” observation time dedicated to characterizing the size and shape of the asteroid before it gets too far from Earth. The result of all this stargazing is that 2024 YR4 is now at a Level 1 on the Torino Scale of NEO collision risk, with a likely downgrade to 0 by the time the asteroid next swings through again in 2028. So, if like us you were into the whole “Fiery Space Rock 2032” thing, you’ll just have to find something else to look forward to.
ssid7 Articles
Rickrolling SSID With ESP32
Reddit user [nomoreimfull] posted code for a dynamic WiFi beacon to r/arduino. The simple, but clever, sketch is preloaded with some rather familiar lyrics and is configured to Rickroll wireless LAN users via the broadcast SSID (service set identifier) of an ESP32 WiFi radio.
The ESP32 and its smaller sibling the ESP8266 are tiny microcontrollers that featuring built-in WiFi support. With their miniature size, price, and power consumption characteristics, they’ve become favorites for makers, hackers, and yes pranksters for a wide variety of projects. They can be easily programmed using their own SDK or through a “board support” extension to the Arduino IDE.
For the dynamic WiFi beacon, the ESP32 is placed into AP (access point) mode and broadcasts its human readable name (SSID) as configured. What makes the SSID dynamic, or rolling, is that the sketch periodically updates the SSID to a next line of text stored within the code. Of course, in the Rickroll prank this means the next line of lyrics from “Never Gonna Give You Up” by Rick Astley himself.
Always a favorite prank, we’ve seen Rickrolls take the form of IR remote controls , free WiFi servers, and coin cell throwies.
Rick Astley picture: Wjack12, CC BY-SA 4.0.
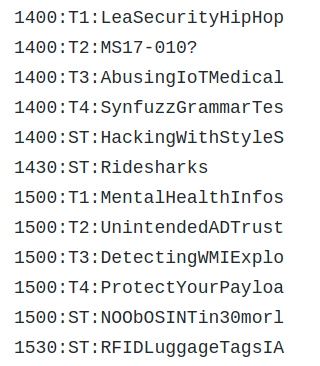
Advertise Your Conference Schedule Via SSID
Whether it’s been a Python script running on a Linux box or an ESP8266, abusing using WiFi SSIDs to convey messages is hardly a new trick. But for DerbyCon 2019, [vgrsec] wanted to do put together something a little unique. Dare we say, even useful. Rather than broadcast out SSID obscenities or memes, this Raspberry Pi created fake WiFi networks that told everyone what talks were coming up.
 The concept here is fairly simple: there’s a text file in
The concept here is fairly simple: there’s a text file in /boot that contains the truncated names of all the talks and workshops in the schedule, one per line, and each line starts with the time that particular event is scheduled for. The script that [vgrsec] wrote opens this text file, searches for the lines beginning with the current time, and generates the appropriate SSIDs. With the number of tracks being run at DerbyCon, that meant there could be as many as five SSIDs generated at once.
Now in theory that would be enough to pull off this particular hack, but there’s a problem. The lack of an RTC on the Raspberry Pi means it can’t keep time very well, and the fact that the WiFi adapter would be busy pumping out SSIDs meant the chances of it being able to connect to the Internet and pull down the current time over NTP weren’t very good.
As the system was worthless without a reliable way of keeping time, [vgrsec] added an Adafruit PiRTC module to the mix. Once the time has been synchronized, the system could then run untethered via a USB battery bank. We might have put it into an enclosure so it looks a little less suspect, but then again, there were certainly far more unusual devices than this to be seen at DerbyCon.
Of course, if you’re OK with just dumping the entire schedule out at once and letting the user sift through the mountain of bogus SSIDs themselves, that’s even easier to accomplish.
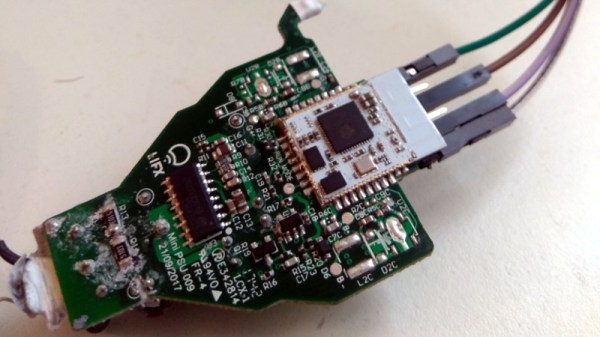
Don’t Toss That Bulb, It Knows Your Password
Whether it was here on Hackaday or elsewhere on the Internet, you’ve surely heard more than a few cautionary tales about the “Internet of Things” by now. As it turns out, giving every gadget you own access to your personal information and Internet connection can lead to unintended consequences. Who knew, right? But if you need yet another example of why trusting your home appliances with your secrets is potentially a bad idea, [Limited Results] is here to make sure you spend the next few hours doubting your recent tech purchases.
In a series of posts on the [Limited Results] blog, low-cost “smart” bulbs are cracked open and investigated to see what kind of knowledge they’ve managed to collect about their owners. Not only was it discovered that bulbs manufactured by Xiaomi, LIFX, and Tuya stored the WiFi SSID and encryption key in plain-text, but that recovering said information from the bulbs was actually quite simple. So next time one of those cheapo smart bulb starts flickering, you might want to take a hammer to it before tossing it in the trash can; you never know where it, and the knowledge it has of your network, might end up.
 Regardless of the manufacturer of the bulb, the process to get one of these devices on your network is more or less the same. An application on your smartphone connects to the bulb and provides it with the network SSID and encryption key. The bulb then disconnects from the phone and reconnects to your home network with the new information. It’s a process that at this point we’re all probably familiar with, and there’s nothing inherently wrong with it.
Regardless of the manufacturer of the bulb, the process to get one of these devices on your network is more or less the same. An application on your smartphone connects to the bulb and provides it with the network SSID and encryption key. The bulb then disconnects from the phone and reconnects to your home network with the new information. It’s a process that at this point we’re all probably familiar with, and there’s nothing inherently wrong with it.
The trouble comes when the bulb needs to store the connection information it was provided. Rather than obfuscating it in some way, the SSID and encryption key are simply stored in plain-text on the bulb’s WiFi module. Recovering that information is just a process of finding the correct traces on the bulb’s PCB (often there are test points which make this very easy), and dumping the chip’s contents to the computer for analysis.
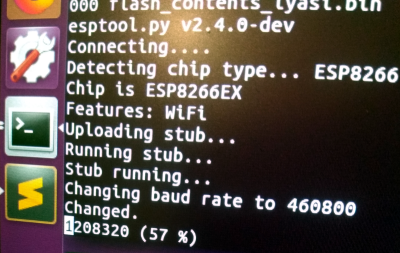
It’s not uncommon for smart bulbs like these to use the ESP8266 or ESP32, and [Limited Results] found that to be the case here. With the wealth of information and software available for these very popular WiFi modules, dumping the firmware binary was no problem. Once the binary was in hand, a little snooping around with a hex editor was all it took to identify the network login information. The firmware dumps also contained information such as the unique hardware IDs used by the “cloud” platforms the bulbs connect to, and in at least one case, the root certificate and RSA private key were found.
On the plus side, being able to buy cheap smart devices that are running easily hackable modules like the ESP makes it easier for us to create custom firmware for them. Hopefully the community can come up with slightly less suspect software, but really just keeping the things from connecting to anything outside the local network would be a step in the right direction.
(Some days later…)
[Limited Results] had hinted to us that he had previously disclosed some vulnerabilities to the bulb’s maker, but that until they fixed them, he didn’t want to make them public. They’re fixed now, and it appears that the bulbs were sending everything over the network unencrypted — your data, OTA firmware upgrades, everything. They’re using TLS now, so good job [Limited Results]! If you’re running an old version of their lightbulbs, you might have a look.
On WiFi credentials, we were told: “In the case where sensitive information in the flash memory wasn’t encrypted, the new version will include encrypted storage processing, and the customer will be able to select this version of the security chips, which can effectively avoid future security problems.” Argue about what that actually means in the comments.
“Hey! Don’t Lock The Door, I’m In Here!”
Those that work in front of a computer for a living spend most of the time making very little sound. Unless you’re a member of the clicky mechanical keyboard club, your working time is a low-observables time during which people can forget about you. You can make sure you’re not overlooked with this smartphone hotspot presence detector.
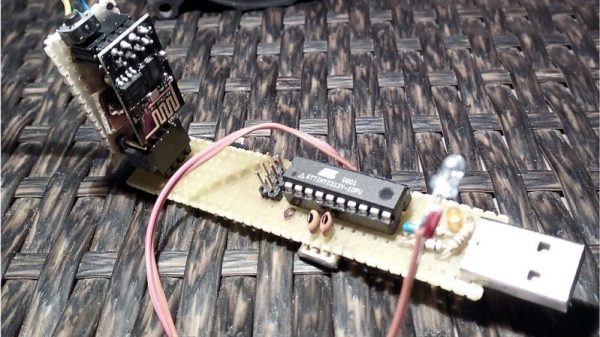
[Emilio Ficara]’s quiet work habits resulted in his housemates locking him in sometimes, to his inconvenience. PIR or microwave occupancy sensors might have worked to fix the problem, except that a few flexing fingers aren’t always enough to trigger them. Luckily, [Emilio] is also wisely distrustful of free WiFi, so his phone is always set up as a mobile hotspot, giving him the means to reliably detect his presence. An ATtiny2313 and an ESP-01 do the business of polling for the SSID of his phone and blinking a bright blue LED by his door for his housemates. It’s not perfect, of course; it could easily be spoofed by anyone else who knows his SSID. But simple works for now.
With almost everyone carrying one now, smartphone detection is a good proxy for the presence of a person. But it doesn’t work in every case, so you may want to familiarize yourself with the aforementioned PIR and microwave methods.
Linger Keeps You Around After You’ve Gone
We’re not sure if this is art, anti-snooping guerilla warfare, or just a cheeky hack, but we do know that we like it! [Jasper van Loenen]’s Linger keeps the SSIDs that your cell phone (for example) spits out whenever it’s not connected to a WiFi network, and replays them after you’re gone.
Some retail stores and other shady characters use MAC addresses and/or the unique collection of SSIDs that your phone submits in probe requests to fingerprint you and track your movement, either through their particular store or across stores that share a tracking provider. Did you know that you were buying into this when you enabled “location services”? Did the tracking firms ask you if that was ok? Of course not. What are you going to do about it?
Linger replays the probe requests of people who have already moved on, making it appear to these systems as if nobody ever leaves. Under the hood, it’s a Raspberry Pi Zero, two WiFi dongles, and some simple Python software that stores probe requests in a database. There’s also a seven-segment display to indicate how many different probe-request profiles Linger has seen. We’re not sure the price point on this device is quite down to “throwie” level, but we’d love to see some of these installed in the local mall. Continue reading “Linger Keeps You Around After You’ve Gone”
Poetic SSIDs
Artists see the same world that the rest of us do. They just see it from a little bit off to the left. Where you see picking an ESSID for your router as being a hassle, or an opportunity to insult your neighbors, [Dmitry], alias [::vtol::] sees a poetry-delivery mechanism.
Based on ESP8266 units, each “poet” has a battery and a switch. Turn it on and it changes its SSID once every ten seconds, feeding everyone who’s listening the next line of a poem. You can’t connect to the network, but you can occasionally hit refresh on your WiFi scanner and read along.
Since they’re so cheap to build, [::vtol::] sees them almost as if they were poetry-throwies. You could easily afford to leave a few around the city, guerilla-style, broadcasting your (slow) message one SSID at a time. We love the video clips (inlined below) of him riding the subway with the device on.