We all know that we’re living in a surveillance state that would make Orwell himself shake his head, but it looks like at least one company in this space has gone a little rogue. According to reports, AI surveillance start-up Flock <<insert gratuitous “What the Flock?” joke here>> has installed at least 200 of its car-tracking cameras on public roads in South Carolina alone. That’s a serious whoopsie, especially since it’s illegal to install anything on state infrastructure without permission, which it appears Flock failed to obtain. South Carolina authorities are making a good show of being outraged about this, but it sort of rings hollow to us, especially since Flock now claims that 70% of the population (of the USA, we presume) is covered by their technology. Also, police departments across the country are in love with Flock’s service, which lets them accurately track the movements of potential suspects, which of course is everyone. No word on whether Flock will have to remove the rogue cameras, but we’re not holding our breath.
java59 Articles
Tetris On An Oscilloscope, The Software Way
When we talk about video games on an oscilloscope, you’d be pardoned for assuming the project involved an analog CRT scope in X-Y mode, with vector graphics for something like Asteroids or BattleZone. Alas, this oscilloscope Tetris (Russian language, English translation) isn’t that at all — but that doesn’t make it any less cool.
If you’re interested in recreating [iliasam]’s build, it’ll probably help to be a retro-oscilloscope collector. The target instrument here is a Tektronix TDS5400, a scope from that awkward time when everything was going digital, but CRTs were still cheaper and better than LCDs. It’s based on a Motorola 68EC040 processor, sports a boatload of discrete ICs on its main PCB, and runs VxWorks for its OS. Tek also provided a 3.5″ floppy drive on this model, to save traces and the like, as well as a debug port, which required [iliasam] to build a custom UART adapter.
All these tools ended up being the keys to the kingdom, but getting the scope to run arbitrary code was still a long and arduous process, with a lot of trial and error. It’s a good story, but the gist is that after dumping the firmware onto the floppy and disassembling it in Ghidra, [iliasam] was able to identify the functions used to draw graphics primitives on the CRT, as well as the functions to read inputs from the control panel. The result is the simple version of Tetris seen in the video below. If you’ve got a similar oscilloscope, the code is up on GitHub.
Care for a more hardware-based game-o-scope? How about a nice game of Pong? Or perhaps a polar breakout-style game is what you’re looking for. Continue reading “Tetris On An Oscilloscope, The Software Way”
Java Is Now On The Nintendo 64!
Whether it’s your favorite programming language, or your favorite beverage, there’s no denying Java is everywhere. Now, it’s even on the Nintendo 64, thanks to the valiant efforts of [Mike Kohn]. Even better, he’s coded a demo to show off its capabilities!
The project took plenty of work. [Mike] went all the way down to the assembly level to get Java code running on the N64. The project builds on the work that he did previously to get Java running on the PlayStation 2. Notably, both the Sony and Nintendo consoles do have some similarities — both are based on MIPS CPUs.
The demo itself is a work of art. It features the typical “3 billion devices run Java” screen, followed by some truly chunky bass and wailing guitar sounds. It’s followed by all the dancing shapes, sinusoidal text, and bright colors you could shake a stick at.
For those interested in the nitty gritty, [Mike] delves deep into the details of what it took to get everything running. That includes both using the code in an emulator, as well as how to get it going on real Nintendo hardware, something we’ve looked at before.
This Week In Security: OpenSSL Fizzle, Java XML, And Nothing As It Seems
The security world held our collective breaths early this week for the big OpenSSL vulnerability announcement. Turns out it’s two separate issues, both related to punycode handling, and they’ve been downgraded to high severity instead of critical. Punycode, by the way, is the system for using non-ASCII Unicode characters in domain names. The first vulnerability, CVE-2022-3602, is a buffer overflow that writes four arbitrary bytes to the stack. Notably, the vulnerable code is only run after a certificate’s chain is verified. A malicious certificate would need to be either properly signed by a Certificate Authority, or manually trusted without a valid signature.
A couple sources have worked out the details of this vulnerability. It’s an off-by-one error in a loop, where the buffer length is checked earlier in the loop than the length variable is incremented. Because of the logic slip, the loop can potentially run one too many times. That loop processes the Unicode characters, encoded at the end of the punycode string, and injects them in the proper place, sliding the rest of the string over a byte in memory as a result. If the total output length is 513 characters, that’s a single character overflow. A Unicode character takes up four bytes, so there’s your four-byte overflow. Continue reading “This Week In Security: OpenSSL Fizzle, Java XML, And Nothing As It Seems”
Finding Digital Solace In An Old Nokia Phone
We don’t have to tell you that the current mobile phone market is a bit bleak for folks who value things like privacy, security, and open source. While there have been a few notable attempts to change things up, from phone-optimized versions of popular Linux distributions to the promise of modular handsets — we still find ourselves left with largely identical slabs released by a handful of companies which often seem to treat the customer as a product.
Instead of waiting for technological relief that may never come, [vrhelmutt] has decided to take matters into their own hands by looking to the past. Specifically, by embracing the relatively uncommon Nokia Asha 210. Released in 2013, this so-called “feature phone” offers a full QWERTY keyboard, Nokia’s Series 40 operating system, WiFi, Bluetooth, and a removable BL-4U battery. Unfortunately, with 2G cellular networks quickly being shut down, it’s not likely to get a signal for much longer (if at all, depending on where you live).
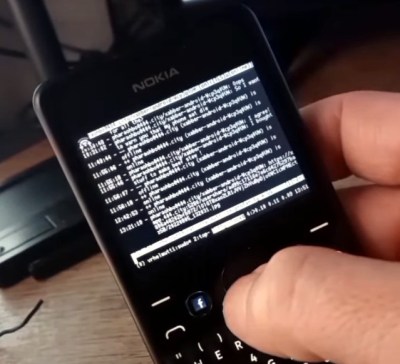 So why would you want to use some weird old Nokia phone in 2022? [vrhelmutt] argues that there’s a whole world of S40 software out there that can still be put to use, ranging from games to SSH clients. It’s also relatively easy to develop your own S40 applications in Java, with the original software development kit still freely available online. Combined with the solid (if considerably dated) hardware, this makes the Nokia Asha 210 a surprisingly compelling choice for a pocket hacking platform.
So why would you want to use some weird old Nokia phone in 2022? [vrhelmutt] argues that there’s a whole world of S40 software out there that can still be put to use, ranging from games to SSH clients. It’s also relatively easy to develop your own S40 applications in Java, with the original software development kit still freely available online. Combined with the solid (if considerably dated) hardware, this makes the Nokia Asha 210 a surprisingly compelling choice for a pocket hacking platform.
Whether you’re looking for a cheap device that will let you chat on IRC from your couch, or want to write your own custom software for controlling your home automation or robotics projects, you might want to check the second-hand market for a Nokia Asha 210. Or if you’re eager to get experimenting immediately, [vrhelmutt] is actually selling these phones pre-loaded with a wide array of games and programs. Don’t consider this to be an official endorsement; frankly we’re not feeling too confident about the legality of redistributing all this software, but at least it’s an option for those looking to get off the modern smartphone thrill-ride.
If you’re looking for something even farther removed from today’s mobile supercomputers, perhaps we could interest you in the Rotary Un-Smartphone.
Continue reading “Finding Digital Solace In An Old Nokia Phone”
Porting DOOM But In The Opposite Direction
DOOM was first released for MS-DOS, and is one of the pillar titles of the broader first-person-shooter genre. It’s also become a bit of a meme for being ported to any and every weird platform under the sun. Now, a group of developers in Costa Rica have found a way to flip that joke around – by porting an old mobile DOOM game back to the PC.
The game in question is DOOM RPG, made for BREW and Java-compatible phones in 2005. A group named GEC.inc has taken that game and ported it to Windows, outlining their work on the Doomworld forums. As with many such projects, the port is freely available, but doesn’t include the raw game files themselves due to copyright. You’ll have to find the gamedata yourself, and combine it with the files the group published on the forum to get it to work on a modern PC.
For those that have missed the turn-based role playing game based in the DOOM universe (Doomiverse?), today is a good day. No longer must you pine for your ancient, crusty Java smartphone of yesteryear. Now you can play the game on a less awful platform, and listen to the unique and compelling MIDI-esque soundtrack.
Doom ports are hot right now, whether it’s to forgotten Apple OSes or Sega arcade hardware. Video after the break.
Continue reading “Porting DOOM But In The Opposite Direction”
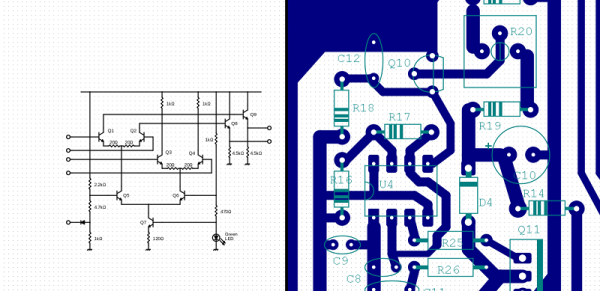
New Release Of FidoCadJ Draws Schematics Everywhere
Do you remember drawing your first schematic? Presumably you used a pen or a pencil and some kind of paper. Schematic capture software, though, makes it so much easier to draw schematics. There are many to choose from, but we spent some time checking out FidoCadJ and found it capable. Of course, there are many other options, but we did like that FidoCadJ runs locally and since it uses Java will run on just about any computer. Since it is open-source, you can modify it and you don’t have to worry about licensing it for your many computers or your team.
The program is a JAR file, and our first attempt to run it ran afoul of our older Java version that was the default Java Runtime Environment. But that was easy to fix, especially since a newer version was there, just not the default.
Continue reading “New Release Of FidoCadJ Draws Schematics Everywhere”