The Nintendo 64 was one of the consoles that properly heralded in the era of 3D gaming. However, its controller is of a design we wouldn’t consider ideal today. For the FPS games that were so popular on the N64, a mouse and keyboard could do much better. [The Hypocaust] set out to make it happen.
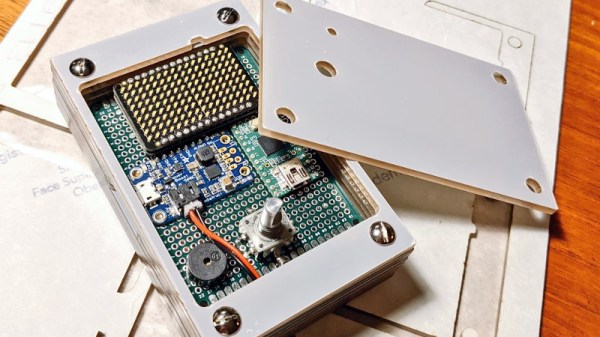
The N64 polls the controller and receives button and analog stick data in return. Four bytes are sent by the controller, with 14 bits covering the buttons and 8 bits covering the horizontal and vertical axes of the analog stick, respectively. Thus, if keyboard presses and mouse movements from a PC could be pumped to a microcontroller which reformatted the data into signals the N64 could understand, everything would work nicely.
Initial attempts to get things working with code borrowed from a [James Read] faced an issue of a 3-second lag between keypresses and actions reaching the N64. Upgrading to a faster microcontroller only made things worse, taking the lag out to a full 16 seconds. The problem? The code borrowed for the project was storing keypresses in a buffer that was creating the delay. Once eliminated, the system worked.
An installer for the software is available, but you’ll have to be comfortable with running a strange executable if you want to use it. We’ve seen similar work before too, such as the USB64 project. Video after the break.