Since the very early 1990s, we have become used to ubiquitous digital mobile phone coverage for both voice and data. Such has been their success that they have for many users entirely supplanted the landline phone, and increasingly their voice functionality has become secondary to their provision of an always-on internet connection. With the 5G connections that are now the pinnacle of mobile connectivity we’re on the fourth generation of digital networks, with the earlier so-called “1G” networks using an analogue connection being the first. As consumers have over time migrated to the newer and faster mobile network standards then, the usage of the older versions has reduced to the point at which carriers are starting to turn them off. Those 2G networks from the 1990s and the 2000s-era 3G networks which supplanted them are now expensive to maintain, consuming energy and RF spectrum as they do, while generating precious little customer revenue.
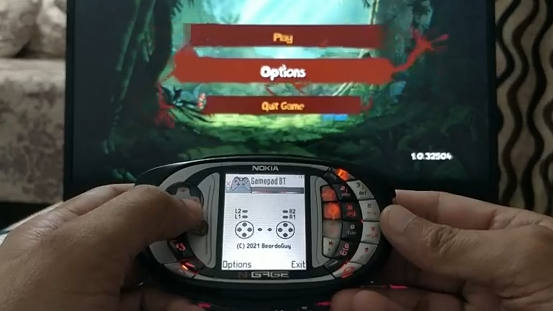
Tech From When Any Phone That Wasn’t A Brick Was Cool

All this sounds like a natural progression of technology which might raise few concerns, in the same way that nobody really noticed the final demise of the old analogue systems. There should be little fuss at the 2G and 3G turn-off. But the success of these networks seems to in this case be their undoing, as despite their shutdown being on the cards now for years, there remain many devices still using them.
There can’t be many consumers still using an early-2000s Motorola Flip as their daily driver, but the proliferation of remotely connected IoT devices means that there are still many millions of 2G and 3G modems using those networks. This presents a major problem for network operators, utilities, and other industrial customers, and raises one or two questions here at Hackaday which we’re wondering whether our readers could shed some light on. Who is still using, or trying to use, 2G and 3G networks, why do they have to be turned off in the first place, and what if any alternatives are there when no 4G or 5G coverage is available? Continue reading “2G Or Not 2G, That Is The Question”