The fourth of five random drawings for Hackaday’s Trinket Everyday Carry Contest was held tonight. The winner is [davish] with his entry, Trinket Watch.
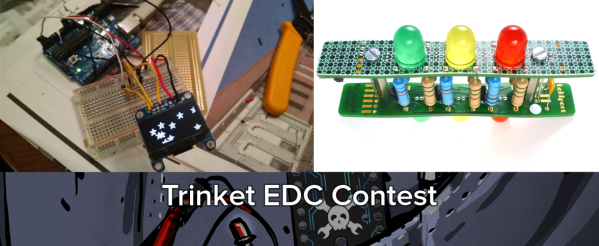
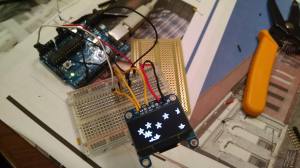 [davish] loves the current crop of smartwatches, but he wants one he can truly call his own. He’s using the Pro Trinket along with an Adafruit 1.3″ OLED for display duties. That little OLED can show a lot more than just numbers though. [davish] already has Adafruit’s logo demo running on the device. Trinket Watch is going to start out as a simple Arduino coded “dumbwatch”. After the basics of time and date are out of the way, [davish] hopes to add a Bluetooth module and turn Trinket Watch into a full-fledged smartwatch.
[davish] loves the current crop of smartwatches, but he wants one he can truly call his own. He’s using the Pro Trinket along with an Adafruit 1.3″ OLED for display duties. That little OLED can show a lot more than just numbers though. [davish] already has Adafruit’s logo demo running on the device. Trinket Watch is going to start out as a simple Arduino coded “dumbwatch”. After the basics of time and date are out of the way, [davish] hopes to add a Bluetooth module and turn Trinket Watch into a full-fledged smartwatch.
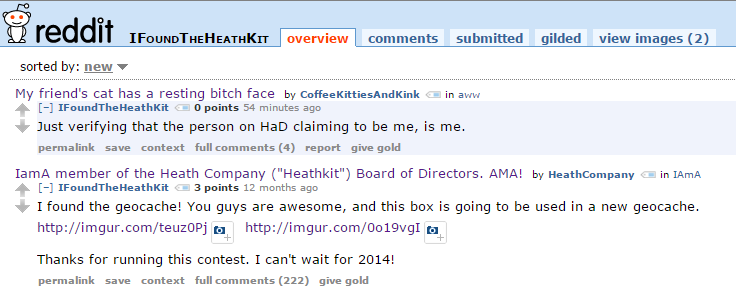
 We hope [davish] enjoys his new Cordwood Puzzle from The Hackaday Store. No jigsaws here, cordwood is a puzzle that involves solder! If you get a piece wrong, it’s time to break out that solder wick and fix your mistake. The puzzle is built using the cordwood assembly technique which was popular in the 1950’s and 1960s. We’re not kidding about it being a puzzle either – there are no instructions for this kit! [davish] will know he’s got it right when all 3 LEDs light up.
We hope [davish] enjoys his new Cordwood Puzzle from The Hackaday Store. No jigsaws here, cordwood is a puzzle that involves solder! If you get a piece wrong, it’s time to break out that solder wick and fix your mistake. The puzzle is built using the cordwood assembly technique which was popular in the 1950’s and 1960s. We’re not kidding about it being a puzzle either – there are no instructions for this kit! [davish] will know he’s got it right when all 3 LEDs light up.
 If you didn’t win this week, all is not lost, you still have one more chance to win a random drawing! Our next drawing will be on 12/30/2014 at 9pm EST. The prize will be a Teensy 3.1 and audio adapter as a prize. To be eligible you need to submit your project as an official entry and publish at least one project log during the week.
If you didn’t win this week, all is not lost, you still have one more chance to win a random drawing! Our next drawing will be on 12/30/2014 at 9pm EST. The prize will be a Teensy 3.1 and audio adapter as a prize. To be eligible you need to submit your project as an official entry and publish at least one project log during the week.
The main contest entry window closes on January 2, 2015 – but don’t wait for the last minute! Hit the contest page and build some awesome wearable or pocketable electronics!