Espressif, the company behind the extremely popular ESP8266 and ESP32 microcontrollers has just announced their latest chip. It’s the ESP32-S2. It’s a powerful WiFi-enabled microcontroller, and this one has support for USB OTG.
Compared to the ESP32 we know and love, there are a few differences. The ESP32-S2 uses a single core Xtensa LX7 core running at up to 240 MHz, where the current ESP32 uses either a single or dual core LX6. The differences between these cores is hidden away in marketing speak and press releases, but it appears the LX7 core is capable of many more floating point operations per cycle: apparently 2 FLOPS / cycle for the LX6, but 64 FLOPS / cycle for the LX7. This is fantastic for DSP and other computationally heavy applications. Other features on the chip include 320 kB SRAM, 128 kB ROM, and 16 kB of RTC memory.
Connectivity for the ESP32-S2 is plain WiFi; Bluetooth is not supported. I/O includes 42 GPIOs, 14 capacitive touch sensing IOs, the regular SPI, I2C, I2S, UART, and PWM compliment, support for parallel LCDs, a camera interface, and interestingly full-speed USB OTG support. Yes, the ESP32-S2 is getting USB, let us all rejoice.
Other features include an automatic power-down of the RF circuitry when it isn’t needed, support for RSA and AES256, and plenty of support for additional Flash and SRAMs should you need more memory. The packaging is a 7 mm x 7 mm QFN, so get out the microscope, enhance your calm, and bust out the flux for this one. Engineering samples will be available in June, and if Espressif’s past performance in supplying chips to the community holds true, we should see some projects using this chip by September or thereabouts.
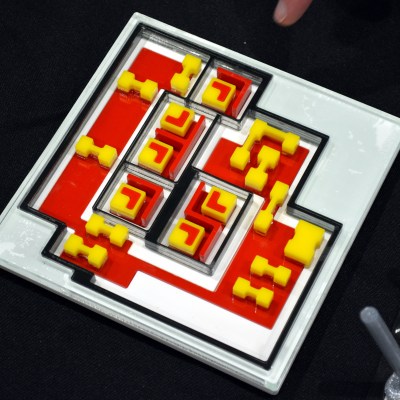
(Banner image is of a plain-old ESP32, because we don’t have any of the new ones yet, naturally.)