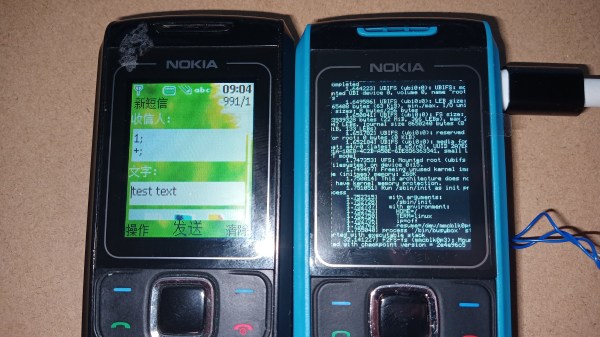
Ever wonder what makes a cellphone’s operating system secure, or what that app you just installed is saying about you behind your back? In a brand new video series, [Jiska] gives us a peek into different topics in smartphone software reverse engineering.
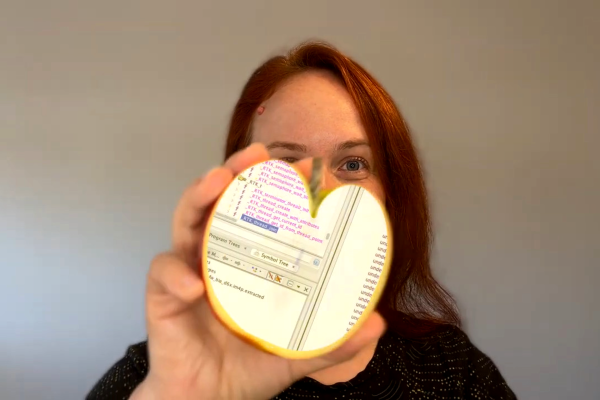
For instance, her latest video, embedded below takes us through some steps to poke at Apple’s RTKit OS, which is the realtime OS that runs inside most of their peripheral devices, including AirPods, but also on their bigger devices too. We don’t know much about RTKit OS, but [Jiska]’s trick in this video is to get a foothold by looking through two different RTKit OS versions and noting which symbols are common — these are probably OS function names. Now you’ve got something to look for.
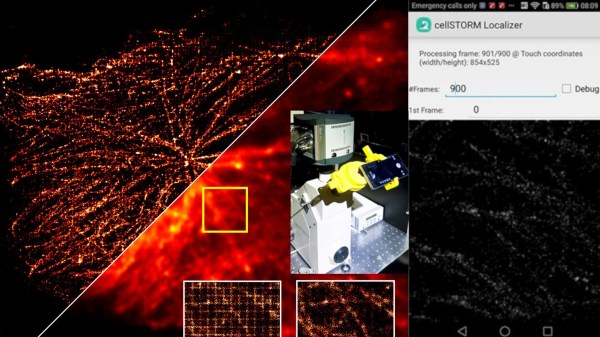
Each of the videos is short, to the point, and contains nice tips for perhaps the intermediate-to-advanced reverser who is looking to get into phones. Heck, even if you’re not, her demonstrations of the Frida dynamic tracing tool are worth your time.
And if you want a longer introduction into the internals of cellphones, we heartily recommend her talk, “All Wireless Stacks Are Broken“.
Continue reading ““Reversing Shorts” Demystify Phone Security”