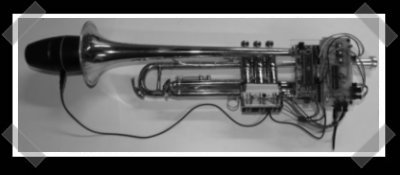
I couldn’t decide between normal and decaffeinated coffee. So to eliminate delays in my morning routine, and decision fatigue, I’ve designed the Schrödinger Quantum Percolator — making the state of my coffee formally undecidable until I drink it.
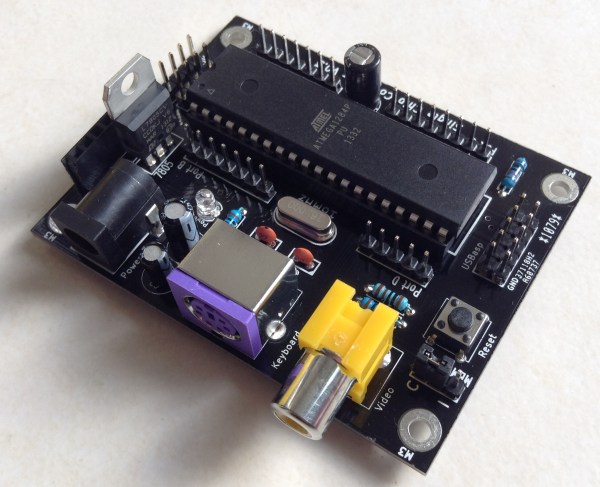
At its core, the Quantum Percolator contains a novel quantum event detector that uses electron tunneling to determine whether to use caffeinated or decaffeinated coffee. The mechanical components are enclosed in an opaque box, so I can’t tell which type of coffee is being used.
The result is coffee that simultaneously contains and does not contain caffeine – at least until you collapse the caffeination probability waveform by drinking it. As the expression goes, you can’t have your quantum superposition of states and drink it too!
Continue reading “Schrödinger Quantum Percolator Makes Half Decent Coffee”