We’ve seen no shortage of projects that use the ESP8266 or ESP32 to add “smart” features to existing home appliances, often by pairing the microcontroller with a radio or IR transmitter. If your device has an existing remote, integrating it into a custom home automation system is often just a matter of getting a few cheap modular components and writing some simple code to glue it all together.
But what if the appliance you want to control doesn’t use a common frequency? That’s a question that [eigma] recently had to answer after finding the remote control for the bedroom ceiling fan was operating at a somewhat unusual 304 MHz. Something like the MAX1472 could probably have been tuned to this frequency, but the chip doesn’t seem to be available in a turn-key module as the popular 315 MHz transmitters are.
 There were a few possible options, including using a software defined radio (SDR), but [eigma] didn’t want to spend a fortune on this project or wait months for parts to get shipped from overseas. The most straightforward solution was to design a custom transmitter tuned to the proper frequency using discrete components; something of a dark art to those of us who’ve been spoiled by the high availability of modular components.
There were a few possible options, including using a software defined radio (SDR), but [eigma] didn’t want to spend a fortune on this project or wait months for parts to get shipped from overseas. The most straightforward solution was to design a custom transmitter tuned to the proper frequency using discrete components; something of a dark art to those of us who’ve been spoiled by the high availability of modular components.
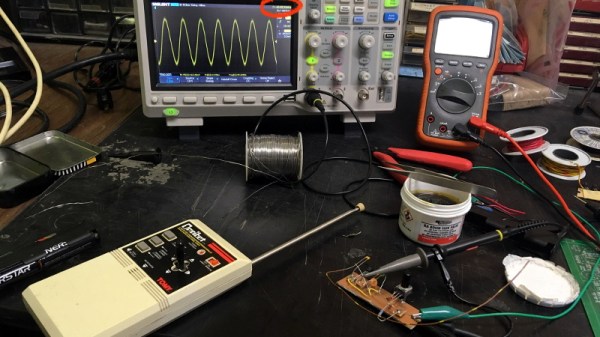
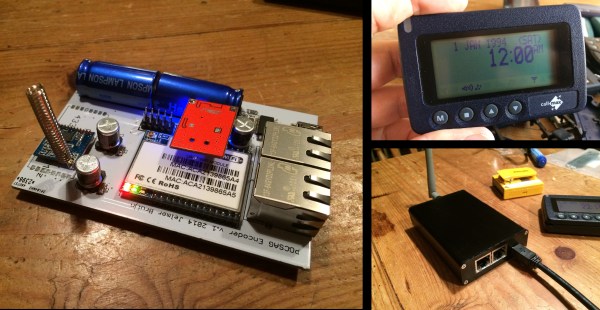
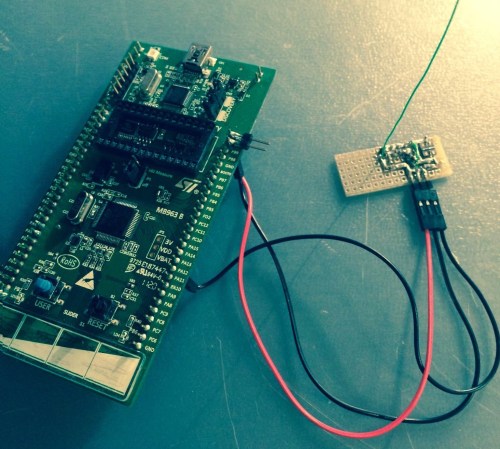
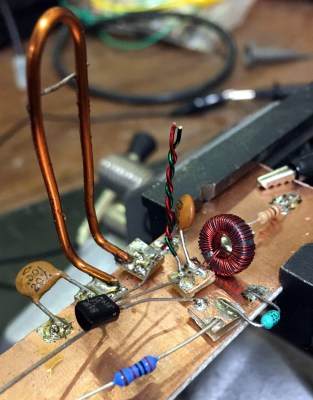
What follows is an fascinating look at the design, testing, and troubleshooting of a truly scratch-built transmitter. You won’t find any ICs here, the carrier signal is generated with just a transistor, some carefully measured pieces of wire, and a handful of passive components. By modulating the signal with an ESP32, [eigma] successfully makes the oddball ceiling fan an honorary member of the Internet of Things.
The write-up that [eigma] has done is an absolutely invaluable resource if you ever find yourself in need of rolling a bespoke transmitter. It easily ranks among some of the most informative radio reverse engineering work we’ve covered, and you’d be wise to file this one away for future reference. That said, most of the newer hardware you’re going to run into will probably be utilizing a widely-supported frequency like 433 MHz.