When you want to fabricate something you either start with something and take away what you don’t want — subtractive manufacturing — or you start with nothing and add material, which is additive manufacturing that we usually call 3D printing. Popular Science recently took a look inside Vital Auto, the British lab that uses 3D printing for high-end concept cars from companies like Rolls-Royce, McLauren, Jaguar, and others. In the video below, [Anthony Barnicott], an engineer for Vital, says that the two technologies — additive and subtractive — work best when used together.
As you might expect, they are not using a $200 FDM printer. They have three Formlabs 3Ls that print with resin and five Formlab Fuse 1 selective laser sintering printers. While metal printers are still uncommon in hacker’s workshops, resin printers are now very affordable although your garage printer is probably a good bit smaller than the 3L’s 335x200x300 mm volume. For comparison, an LCD-based AnyCubic Photon X provides just 165x132x80 mm. Of course, you’re looking at about $11,000 for the dual-laser 3L versus about $240 for the Photon.
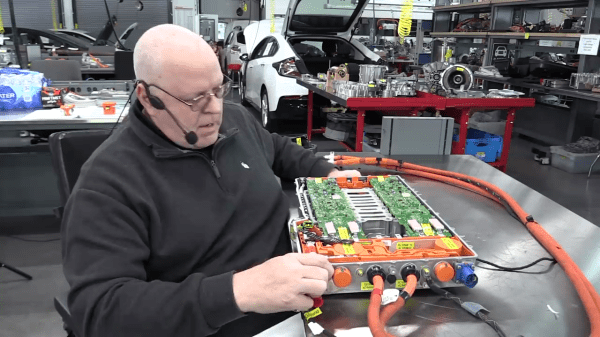
Vital started building the EP9 electric car concept for NIO, an electric car maker in China. You can imagine that modern manufacturing machines make it possible to create more sophisticated concept cars faster. How many times do you want to tweak a part that takes a machinist eight hours to produce? But if you can just let a machine run overnight and get the result in the morning, you are more likely to change and refine the part.
Vital Auto is an interesting look at how professional fabrication shops are using the same technologies we do, at least at the core. We’ve noted before how these same technologies are making homebrew projects look better than some commercial products not long ago. You can print big things if you break them up, of course. Or, break the bank and buy a really big printer.