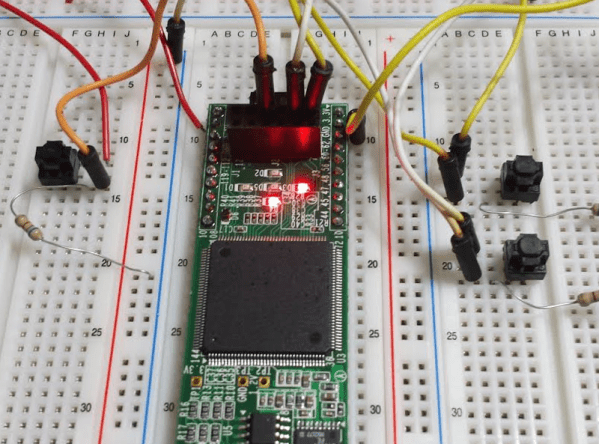
There’s an old joke about how can you find the height of a building using a barometer. One of the punchlines is to drop the barometer from the roof and time how long it takes to hit the ground. We wonder if [Alexlao512] had that in mind when he wrote a post about unconventional uses of FPGAs. Granted, he isn’t dropping any of them off a roof, but still. The list takes advantage of things we usually try to avoid such as temperature variation, metastability, and the effects of propagation delays.
For example, you probably know that hooking up an odd number of inverters into a loop forms an oscillator—the so-called ring oscillator. The post discusses how you can use an oscillator like that to measure propagation delay or even as a strain gauge. If you put pressure on the FPGA chip, the frequency of the ring oscillator will subtly vary.