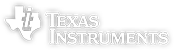
A car from 1940 would have been an almost completely mechanical device. These days though, a car without electricity wouldn’t run. It’s not the engine – it’s the computers; the design details of which automotive manufacturers would love to keep out of the hands of hardware hackers like us. [Mastro Gippo] wanted to build a small and powerful CAN bus reverse engineering tool, and the Crunchtrack hits it out of the park. It’s a CAN bus transceiver, GPS receiver, and GSM modem all wrapped up into a single tiny device that fits under your dash.
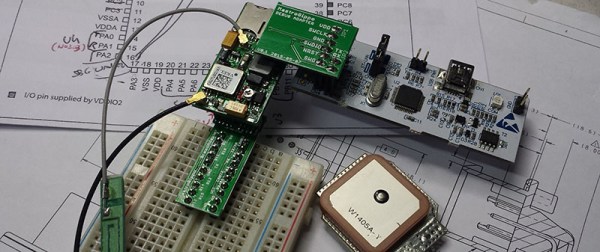
[Mastro] has a slight fetish for efficiency and tiny, tiny devices, so he’s packaging everything inside the shell of a standard ELM327 Bluetooth adapter. This is a device that can fit in the palm of your hand, but still taps a CAN bus (with the help of a computer), receives GPS, and sends that data out over cell phone towers.
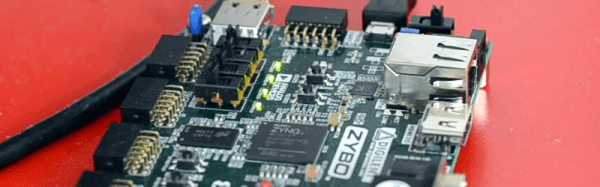
The device is based on the STM32 F3 ARM microcontroller (with mbed support), a ublox 7 GPS module, and an SIM800 GSM module, but the story doesn’t stop with hardware. [Mastro] is also working on a website where reverse engineering data can be shared between car hackers. That makes this an excellent Hackaday Prize entry, and we can’t wait to see where it goes from here.







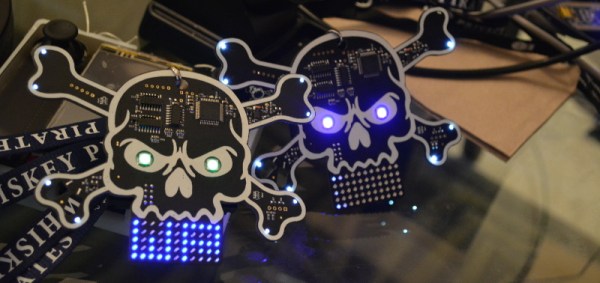


![DSC_0528 Gorgeous text treatment on back of this badge is indicative of [True's] mastery](https://i0.wp.com/hackaday.com/wp-content/uploads/2015/08/dsc_0528.jpg?w=262&h=174&ssl=1)