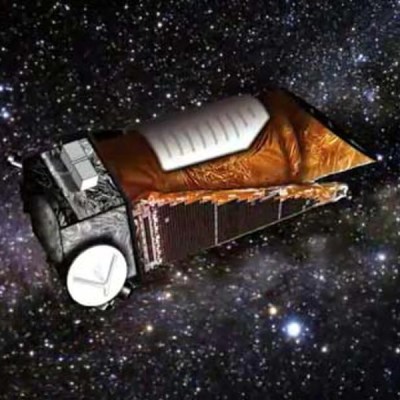
Since its launch in March 2009, the Kepler Space Telescope has provided us with an incredible amount of data about exoplanets within our galaxy, proving these worlds are more varied and numerous than we could ever have imagined. Before its launch we simply didn’t know how common planets such as ours were, but today we know the Milky Way contains billions of them. Some of these worlds are so hot they have seas of molten rock, others experience two sunsets a day as they orbit a pair of stars. Perhaps most importantly, thousands of the planets found by Kepler are much like our own: potentially playing host to life as we know it.
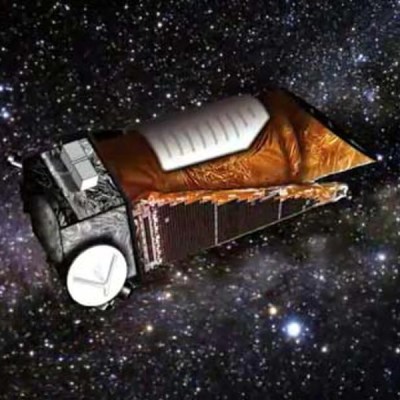 Kepler lived a fruitful life by any metric, but it hasn’t been an easy one. Too far into deep space for us to repair it as we did Hubble, hardware failures aboard the observatory nearly brought the program to a halt in 2013. When NASA announced the spacecraft was beyond hope of repair, most assumed the mission would end. Even by that point, Kepler was an unqualified success and had provided us with enough data to keep astronomers busy for years. But an ingenious fix was devised, allowing it to continue collecting data even in its reduced capacity.
Kepler lived a fruitful life by any metric, but it hasn’t been an easy one. Too far into deep space for us to repair it as we did Hubble, hardware failures aboard the observatory nearly brought the program to a halt in 2013. When NASA announced the spacecraft was beyond hope of repair, most assumed the mission would end. Even by that point, Kepler was an unqualified success and had provided us with enough data to keep astronomers busy for years. But an ingenious fix was devised, allowing it to continue collecting data even in its reduced capacity.
Leaning into the solar wind, Kepler was able to use the pressure of sunlight striking its solar panels to steady itself. Kepler’s “eyesight” was never quite the same after the failure of its reaction wheels, and it consumed more propellant than originally intended to maintain this careful balancing act, but the science continued. The mission that had already answered many of our questions about our place in the galaxy would push ahead in spite of a failure which should have left it dead in space.
As Kepler rapidly burned through its supply of propellant, it became clear the mission was on borrowed time. It was a necessary evil, as the alternative was leaving the craft tumbling through space, but mission planners understood that the fix they implemented had put an expiration date on Kepler. Revised calculations could provide an estimate as to when the vehicle would finally run its tanks dry and lose attitude control, but not a definitive date.
For the last several months NASA has known the day was approaching, but they decided to keep collecting data until the vehicle’s thrusters sputtered and failed. So today’s announcement that Kepler has at long last lost the ability to orient itself came as no surprise. Kepler has observed its last alien sunset, but the search for planets, and indeed life, in our corner of the galaxy doesn’t end today.
Continue reading “Kepler Closes Eyes After A Decade Of Discovery” →