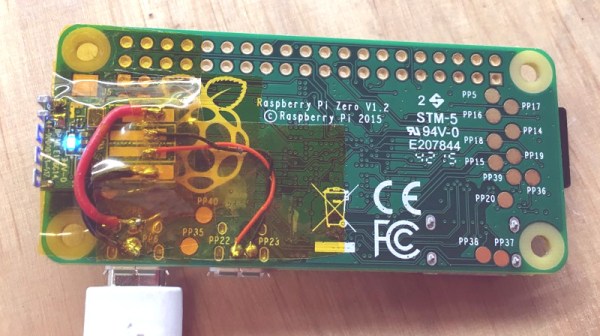
And we have the first Raspberry Pi Zero hack! In less than 72 hours from the official release announcement [Shintaro] attached an Edimax WiFi USB Adapter directly to the USB solder pads on the Pi Zero. He couldn’t bear to disturb the small dimensions of the Pi Zero by using the USB On-the-Go (OTG). The OTG is needed to convert the micro-USB connector on the board to a full USB-A connector.
The case was removed from the Edimax and the device and Zero wrapped in Kapton to insulate the exposed solder points. Power was taken from the PP1 and PP6 points on the back of the board. These are the unregulated inputs from the USB power so should be used with caution. Some cheap USB power supplies can put out more that 5 volts when first connected and that might let the smoke out of a device.
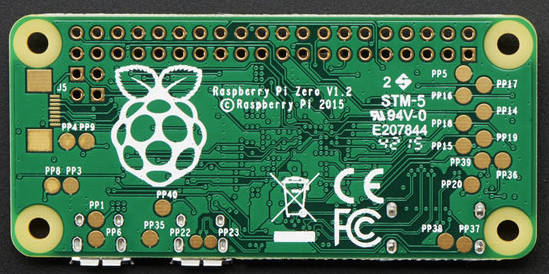
The data wires were connected to PP22 and PP23, also on the back, and behind the USB data connector. Since USB is a differential signal these wires were carefully kept of equal length to avoid distorting the signal.
An SD card was created and edited on a Raspberry Pi B 2 to set the WiFi credentials. Inserted into the Zero it booted fine and started up the WiFi network connection.
Congratulations, [Shintaro] for the first Hackaday Raspberry Pi Zero hack. Is that a Hack-a-Zero-Day hack?


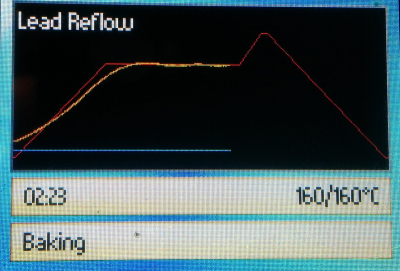 The controller was a mashup of the existing oven’s keypad and an add-on LCD display (see right). One thing we didn’t see was a schematic. Of course, you can read the code and figure out how it is all connected and (unless you use the exact same oven) you are probably going to need to modify things to suit your particular setup, anyway.
The controller was a mashup of the existing oven’s keypad and an add-on LCD display (see right). One thing we didn’t see was a schematic. Of course, you can read the code and figure out how it is all connected and (unless you use the exact same oven) you are probably going to need to modify things to suit your particular setup, anyway.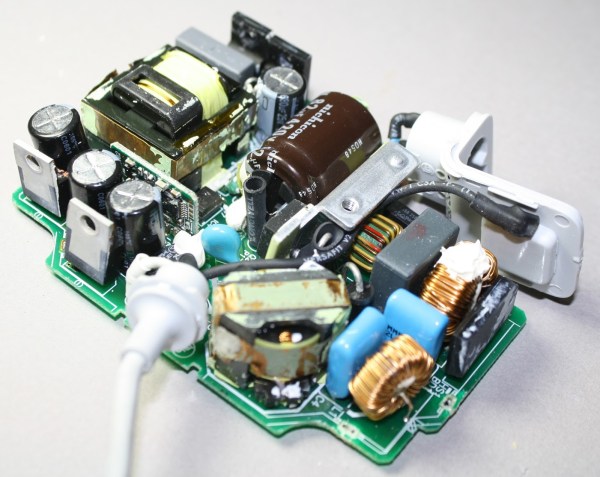
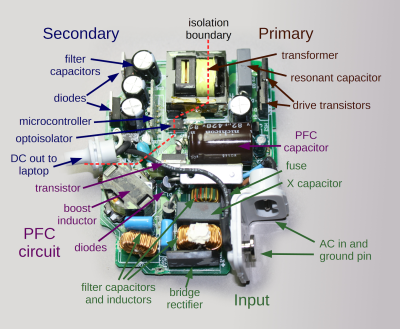

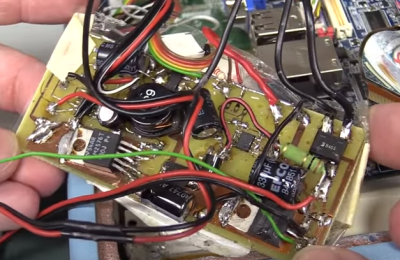 The tablet is based upon an off-the-shelf embedded PC motherboard and touchscreen controller. [Dave] took some offense at the hacked up USB connector on the touchscreen. We have to disagree with [Dave] a bit here, as the video seems to show that a standard mini-b connector wouldn’t have fit inside the tablet’s case. There’s no excuse for the USB cable shield draped over the bare touch controller board though. Things go downhill from there. The tablet’s power supply is best described as a bizarre mess. Rather than use a premade DC to DC converter, whoever built this spun their own switch mode power supply on a home etched board. The etching job looks good, but everything else, including the solder job, is beyond terrible. All the jumps and oddly placed components make it look like a random board from the junk bin was used to build this supply.
The tablet is based upon an off-the-shelf embedded PC motherboard and touchscreen controller. [Dave] took some offense at the hacked up USB connector on the touchscreen. We have to disagree with [Dave] a bit here, as the video seems to show that a standard mini-b connector wouldn’t have fit inside the tablet’s case. There’s no excuse for the USB cable shield draped over the bare touch controller board though. Things go downhill from there. The tablet’s power supply is best described as a bizarre mess. Rather than use a premade DC to DC converter, whoever built this spun their own switch mode power supply on a home etched board. The etching job looks good, but everything else, including the solder job, is beyond terrible. All the jumps and oddly placed components make it look like a random board from the junk bin was used to build this supply.
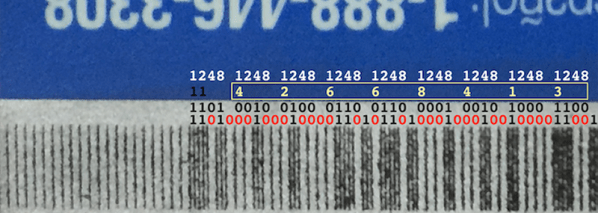
 The electronics for the MagSpoof are incredibly simple. Of course a small microcontroller is necessary for this build, and for the MagSpoof, [Samy] used the ATtiny85 for the ‘larger’ version (still less than an inch square). A smaller, credit card-sized version used an ATtiny10. The rest of the schematic is just an H-bridge and a coil of magnet wire – easy enough for anyone with a soldering iron to put together on some perfboard.
The electronics for the MagSpoof are incredibly simple. Of course a small microcontroller is necessary for this build, and for the MagSpoof, [Samy] used the ATtiny85 for the ‘larger’ version (still less than an inch square). A smaller, credit card-sized version used an ATtiny10. The rest of the schematic is just an H-bridge and a coil of magnet wire – easy enough for anyone with a soldering iron to put together on some perfboard.