[Martin Fasani] has set out to build a beautiful low power E-Ink Calendar he can hang on his wall. But perhaps more importantly, the work he has done makes it easier for everyone in the future to have a e-ink display. Many battery-powered e-ink projects connect to some server, download a bitmap image, display the new image, and then go into a deep sleep power mode. [Martin’s] project is no different, but it uses a handy microservice that does the conversion and rendering for you.
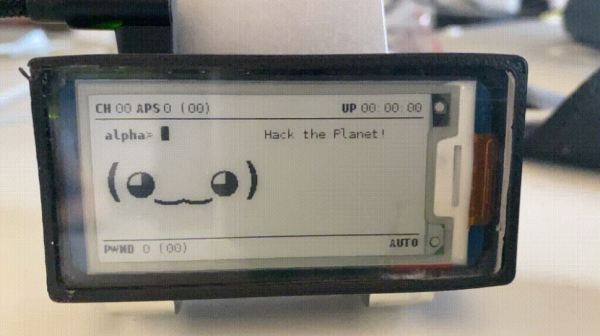
The firmware for this ESP32/ESP32S2 based calendar is open sourced on GitHub, with a version based on the Arduino framework as well as the native ESP-IDF framework. One particularly fantastic part of the firmware is a C++ component called CalEPD that drives e-paper displays. CalEPD extends the Adafruit_GFX class and is broken out in a separate repo, making it easy to consume on other projects. Since this supports dozens of different e-paper displays, this simplifies the process of building a calendar with different screens. The firmware includes a Bluetooth setup flow from a smartphone or tablet. This means you can quickly configure how often it wakes up, what it queries, and other important features.
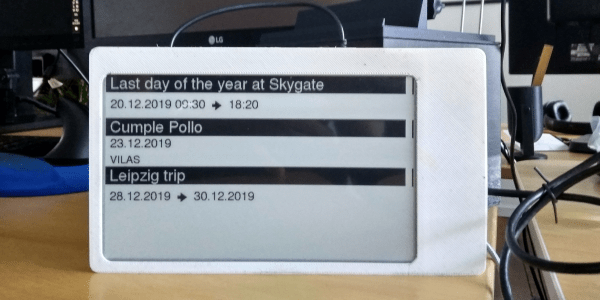
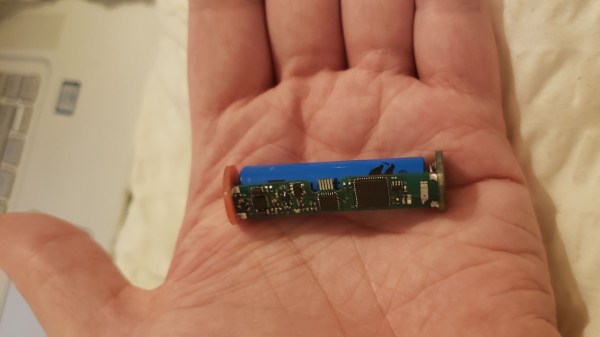
The hardware shown in the demo video has a 7.5″ Waveshare screen with 800 x 400 resolution nestled inside a 3D-printed shell. There is also a 5,000 mAh battery with an ESP32 TinyPICO powering the whole system. The TinyPICO was picked for its incredible deep sleep power consumption. All this fits into a frame just 11 mm thick, for which STL files are available. [Martin] continues to work on this calendar display and has recently added support for FocalTech touch panel controllers. We’re excited to see where he takes it next!
This isn’t the first e-ink display project we’ve seen but this is a great reference to build your own. If you need another good starting point, this weather display might give you that little bit of inspiration you need.