After the alleged drone attacks on London Gatwick airport in 2018 we’ve been on the look out for effective countermeasures against these rogue drone operators. An interesting solution has been created by [Ogün Levent] in Turkey and is briefly documented on in his Dronesense page on Crowdsupply. There’s a few gaps in the write up due to non-disclosure agreements, but we might well be able to make some good guesses as to the missing content.
Not one, but two LimeSDRs are sent off into the air onboard a custom made drone to track down other drones and knock them out by jamming their signals, which is generally much safer than trying to fire air to air guided missiles at them!
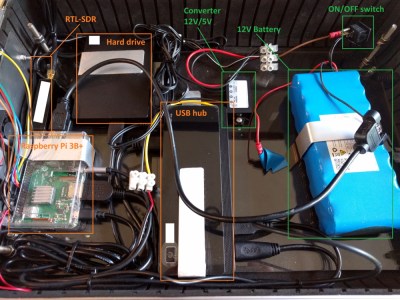
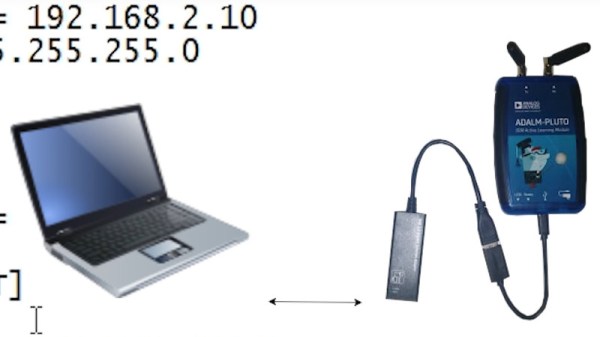
 The drone hardware used by [Ogün Levent] and his team is a custom-made S600 frame with T-Motor U3 motors and a 40 A speed controller, with a takeoff weight of 5 kg. An Adventech single board computer is the master controller with a Pixhawk secondary and, most importantly, a honking great big 4 W, 2.4 GHz frequency jammer with a range of 1200 meters.
The drone hardware used by [Ogün Levent] and his team is a custom-made S600 frame with T-Motor U3 motors and a 40 A speed controller, with a takeoff weight of 5 kg. An Adventech single board computer is the master controller with a Pixhawk secondary and, most importantly, a honking great big 4 W, 2.4 GHz frequency jammer with a range of 1200 meters.
The big advantage of sending out a hunter drone with countermeasures rather than trying to do it on the ground is that, being closer to the drone, the power of the jammer can be reduced, thus creating less disturbance to other RF devices in the area – the rogue drone is specifically targeted.
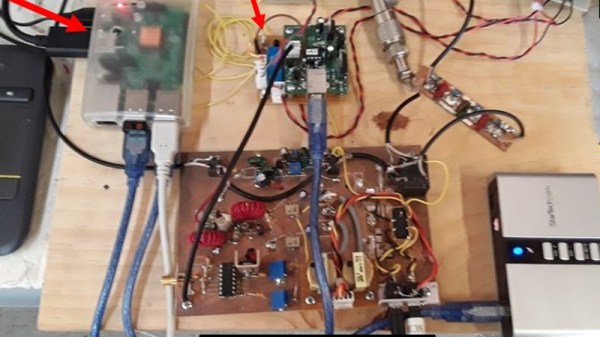
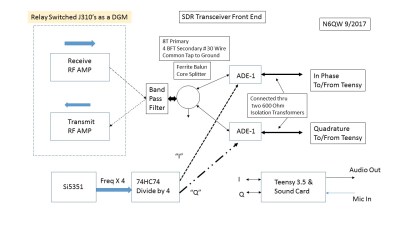
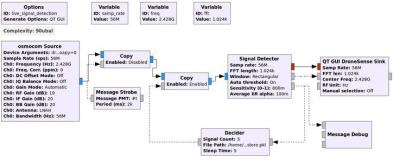 One of the LimeSDRs runs a GNU radio flowgraph with a specially designed block for detecting the rogue drone’s frequency modulation signature with what seems to be a machine learning classification script. The other LimeSDR runs another *secret* flowgraph and a custom script running on the SBC combines the two flowgraphs together.
One of the LimeSDRs runs a GNU radio flowgraph with a specially designed block for detecting the rogue drone’s frequency modulation signature with what seems to be a machine learning classification script. The other LimeSDR runs another *secret* flowgraph and a custom script running on the SBC combines the two flowgraphs together.
So now it’s the fun part, what does the second LimeSDR do? Some of the more obvious problems with the overall concept is that the drone will jam itself and the rogue drone might already have anti-jamming capabilities installed, in which case it will just return to home. Maybe the second SDR is there to track the drone as it returns home and thereby catch the human operator? Answers/suggestions in the comments below! Video after the break. Continue reading “Drone On Drone Warfare, With Jammers”