$30,000?
Is it art or is it a puzzle? Well, it functions as a game but it’s certainly a work of art and priced accordingly. The Superplexus was featured in Make Mazine and Hammacher Schlemmer sells it for thirty grand (you can’t just click to add it to your cart though). Think of the work that went into developing this! [via The Awesomer]

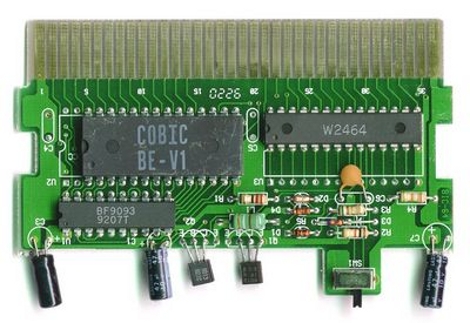
Rollable Display Update
[SeBsZ] continues work on his rollable display matrix. He’s got twenty five controller boards now and has them working as a matrix. We originally covered this in January but now it’s much easier to see how this can be made portable by mounting it on fabric or canvas. Check out the demo video if your interested.

Security testing suite
BackTrack 4 final has been released. If you didn’t like it when it was rough around the edges, you should give it another try. This lean and mean Linux ditro is made for security testing and is approachable for noob and pro alike. [Thanks Steve]

Power on the go
[Csae] uses this portable power center to fire up some studio strobes outside. It consists of a case, an uninterruptible power supply, and a couple of extension cords all hacked together into one. At first you might think this is a bit ghetto but it’s portable and it does what is intended.

Happy Valentine’s Day
Giving this LED-heart adorned shirt as a gift is sure to make your Valentine head for the hills. This project’s a few year’s old, but gawdy T-shirts never go out of style, right?