If you’ve never considered roasting your own coffee at home, you may be surprised to learn that it can be done in a few minutes with a regular popcorn popper and not much else. After all, you only really need two things to roast coffee: heat, and constant agitation to distribute that heat evenly. While the popcorn popper provides both, it’s easy to end up with semi-uneven roasts, probably because the beans are mostly just spinning around and not being tossed as well as they could be. Eventually, one might want a more advanced machine, and that’s where something like [Larry Cotton]’s latest wobble disk roaster can step in.
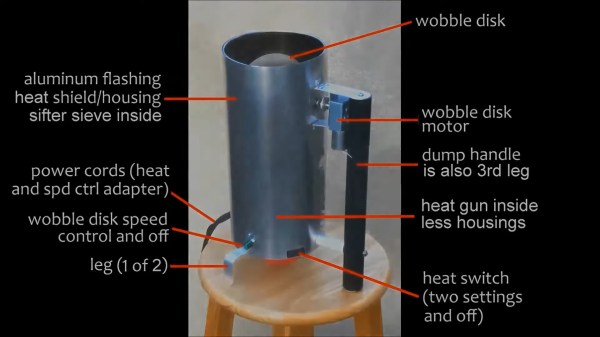
For starters, this machine roasts more beans than the average popcorn popper in a single throw — the maximum is 350g, or just over three-quarters of a full pound, which is way more than the average popcorn machine will hold. It essentially consists of a heat gun pointed upwards at a sieve full of green coffee beans that are being constantly pushed around by a motorized wobbling disk. As the heat blows, the large metal disk does figure eights through the beans, keeping the heat nice and even. So where does the red ball come in? It’s at the bottom, keeping the flying bean skins (chaff) from entering the heat gun’s fan motor.
Toward the end of the short video after the break, you’ll see a diagram showing all the parts of this roaster. If that’s not enough for you, here’s a build guide for a previous wobble disk roaster (PDF) that should be quite helpful in building either version.
If you want to see some of Larry’s previous machines, we’ve got ’em. And then you can let Hackaday Editor-in-Chief [Elliot Williams] tell you all about roasting at home.
Continue reading “Follow The Red Ball Wobble Disk Roaster To Coffee Excellence”






 He was born in Glasgow in 1821 and was the son of a successful shipbuilder, Robert Napier, into whose business he followed once he’d received his education. He’s probably most well known today for his work in nautical engineering and for inventing
He was born in Glasgow in 1821 and was the son of a successful shipbuilder, Robert Napier, into whose business he followed once he’d received his education. He’s probably most well known today for his work in nautical engineering and for inventing