Of all the things which are annoying about the modern World Wide Web, the need to create and remember countless passwords is on the top of most people’s lists. From dozens of passwords for everything from social media sites to shopping, company, and productivity-related platforms like Github, a large part of our day is spent dealing with passwords.
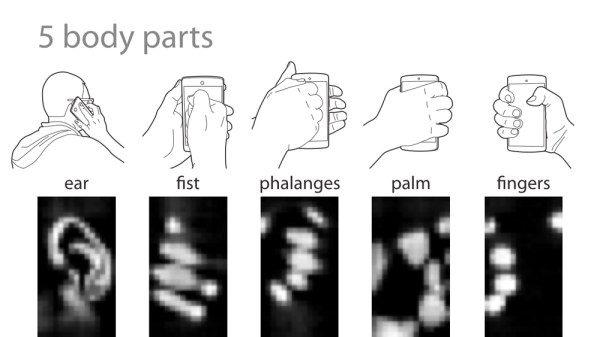
While one can totally use a password manager to streamline the process, this does not absolve you from having to maintain this list and ensure you never lose access to it, while simultaneously making sure credentials for the password manager are never compromised. The promise of password-less methods of authentication is that of a world where one’s identity is proven without hassle, and cannot ever be stolen, because it relies on biometrics and hardware tokens instead of an easily copied password.
The FIDO2 project promises Web Authentication that means never entering a password into a website again. But like everything, it comes with some strings attached. In this article, we’ll take a look at how FIDO2 plans to work and how that contrasts with the state of security in general.
Continue reading “FIDO2: The Dream Of Password-Free Authentication On The WWW”