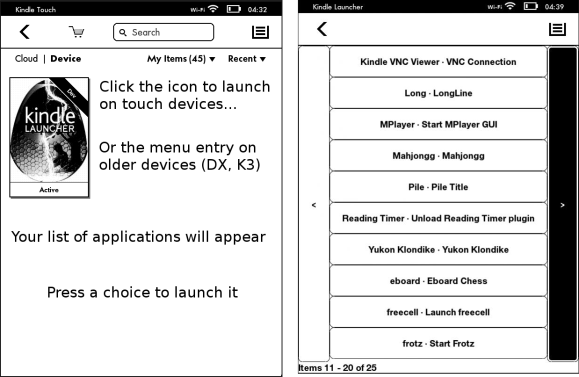
People love books, and if you’re anything like [tjaap]’s girlfriend, you may easily devour your eighty books and more a year. Maybe to keep better track of time during her reading sessions, her wish was to get a clock for the living room, so [tjaap] stepped up. Being a maker at heart, he decided to skip the ready-made options, and instead build one in the most fitting way imaginable: by displaying the time as literary quotes on a jailbroken Kindle.
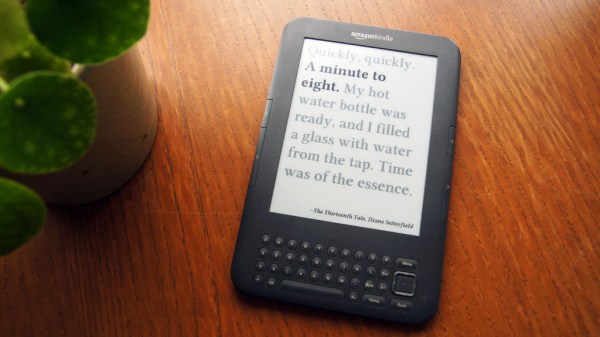
Unlike your average word clock, [tjaap]’s literary clock displays (almost) every minute a different sentence that, in one form or another, contains the current time. Thanks to the internet, he didn’t have to compile the whole list of book quotes for each and every minute of the day by himself, but it still required some work to put it all in the form he needed. Eventually he had a script that converted each quote into an image, and a shell script on the Kindle to display them according to the time. As a bonus, the origin of the quote is displayed only optionally, turning the clock into a simple trivia quiz along the way.
It shows that themed, personalized clocks are always a great subject for a gift, just like the one made from analog meters we saw around Father’s Day.