[ananords] and his girlfriend wanted to make a simple and easy to use music player for her grandmother. Music players like CD players and MP3s have gotten just a bit too difficult to handle, so they wanted to find a much simpler solution.
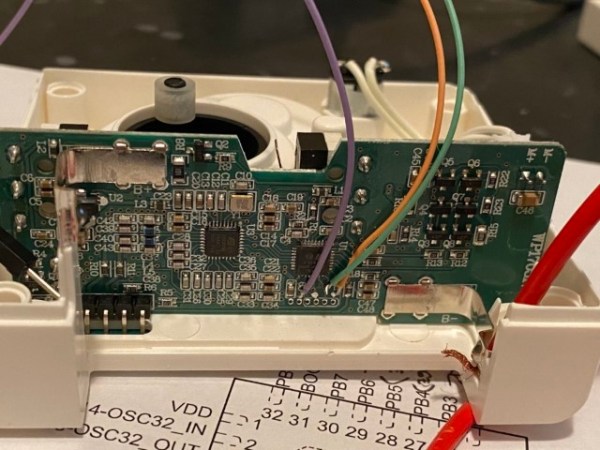
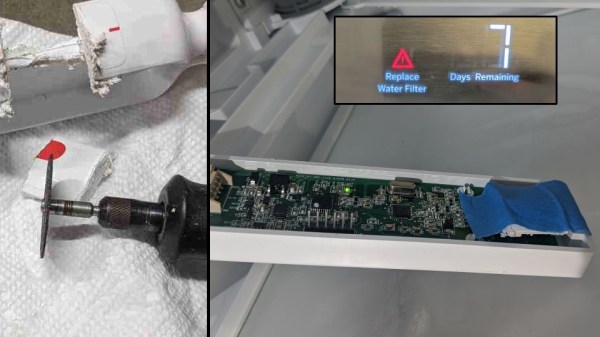
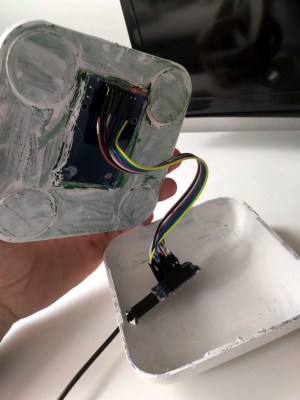
They conceived the idea of creating a little jukebox called Juuk, with a simple and easy to use interface. They created individual RFID cards with the artist’s photo on the front face, making it easy to select different options from the music library. Juuk has a built-in RFID reader that will recognize each RFID card and play the appropriate musical number from an SD card.
This simple interface is much more user-friendly than those awful touchscreen devices that we’re all forced to fiddle with today and also has a cool retro appeal that many of our readers are sure to appreciate. Juuk also has a pretty ergonomic interface with a big, easy-to-use knob for controlling the volume and two appropriately illuminated buttons, one green and one red, for simple stop and play options.
We love when our hacks are able to blend form with function and emphasize high usability. Check out some of our other assistive tech on the blog.
Continue reading “Juuke – An RFID Music Player For Elderly And Kids”