Depending upon where in the world you live, AC mains frequency is either 50Hz or 60Hz, and that frequency is maintained accurately enough over time that it can be used as a time reference for a clock. Oddly it’s rarely exactly that figure though, instead it varies slightly with load on the network and the operators will adjust it to keep a constant frequency over a longer period. These small variations in frequency can easily be measured, and [jp3141] has created a circuit that does exactly that.
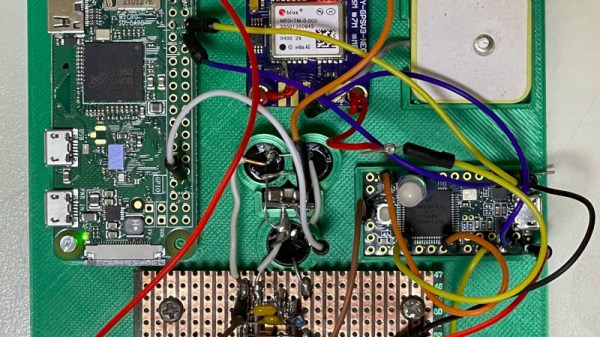
It’s a surprisingly straightforward device, in which a Teensy takes its power supply from a very conventional if now a little old-school mains transformer, rectifier, and regulator. A sample of the AC from the transformer passes through a low-pass filer and a clamp, and thence to the Teensy where it is fed into one of the on-board comparators from which its period is measured using one of the timers. Even then the on-board crystal isn’t considered accurate enough, so it is in turn disciplined by a 1 pulse per second (PPS) signal from a GPS receiver.
The Teensy then reports its readings over a serial line every five seconds to a Raspberry Pi, which collates and graphs the data. In case you are wondering what the effect of mains frequency variations might be, we once covered the story of how an entire continent lost six minutes.