Years before Steve Jobs showed off the first iPhone, the BlackBerry was already the must-have accessory for mobile professionals. Back then, nobody was worried about watching movies or playing the latest games on their mobile devices, they just wanted a secure and fast way to send and receive email on the go. For that, the BlackBerry was king.
Fast forward to today, and the company is just a shell of what it once was. They don’t even bother making their own hardware anymore. Over the last several years they’ve opted to partner with a series of increasingly obscure manufacturers to produce a handful of lackluster Android phones so they still have something to sell to their dwindling userbase. Anyone excited about the new 5G BlackBerry being built by Texas start-up OnwardMobility? Did you even know it was in the works before now?
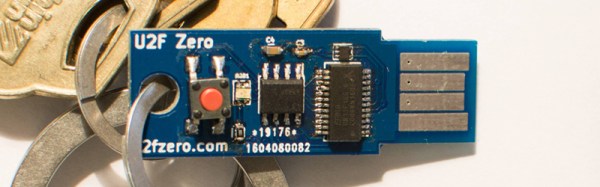
But this article isn’t about BlackBerry phones. It’s about something that’s even more irrelevant to consumers: the BlackBerry Smart Card Reader. Technically, this little device isn’t dependent on the phones of the same name, but it makes sense that Research In Motion (which eventually just renamed itself to BlackBerry Limited) would market the gadget under the brand of their most popular product. Though as you might expect, software was available to allow it to work with the BlackBerry phone that you almost certainly owned if you needed a dedicated smart card reader.
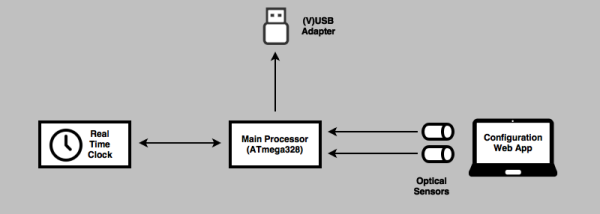
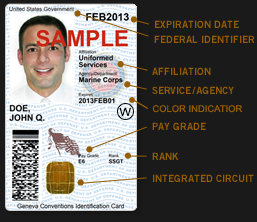
For those who might not be aware, a smart card in this context is a two-factor authentication token contained in an ID card. These are used extensively by organizations such as the Department of Defense, where they’re known as Common Access Cards, that require you to insert your ID card into a reader before you can log into a secure computer system. This sleek device was marketed as a portable reader that could connect to computers over USB or Bluetooth. Worn around your neck with the included lanyard, the battery-powered reader allowed the card itself to remain on the user’s body while still being readable by nearby devices.
Civilians will recognize the basic technology from modern “Chip and PIN” debit and credit cards, but we’ve never had to stick one of those into our laptop just to log in. To be sure, the BlackBerry Smart Card Reader was never intended for the average home computer user, it was sold to companies and organizations that had tight security requirements; which just so happened to be the same places that would likely already be using BlackBerry mobile devices.
Of course, times and technology change. These devices once cost $200 apiece and were purchased in vast quantities for distribution to trusted personnel, but are now all but worthless. Even in new and unopened condition, they can be had for as little as $10 USD on eBay. For that price, it’s certainly worth taking a peek inside. Perhaps the hacker community can even find new applications for these once cutting-edge devices.