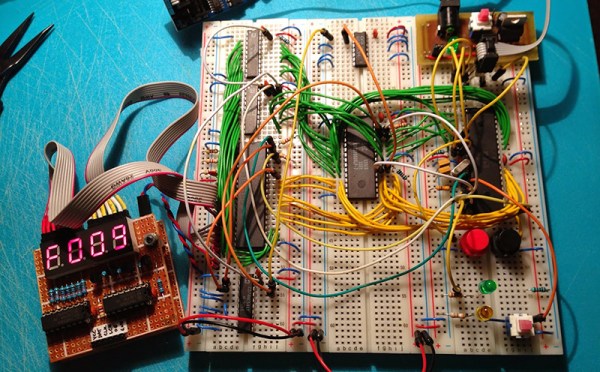
Everyone is having a go at building their own 8-bit 80s-era microcomputer now, and [Petri] thought he would throw his hat into the ring with ERIC-1, a homebrew, 6502-based computer that’s running at about 2MHz.
We’re about 30 or 40 years ahead of the game compared to the old-school 6502 designs, and [Petri] decided to capitalize on that. Instead of a separate ROM, VIA, and other peripherals, [Petri] is connecting a microcontroller directly to the data and address pins. This is a technique we’ve seen before, and [Petri] is doing it right: the micro and 6502 share 64k of RAM, with the ROM stored in the micro’s Flash. Video (PAL in this case) is handled by the ATMega, as is clocking and halting the CPU.
There were a few changes [Petri] made along the way to make this microcomputer a little more useful. One of the biggest changes was switching out the old NMOS Rockwell 6502 with the modern CMOS W65C02 from Western Design Center. The CMOS variant is a fully static design, keeping the registers alive even if the clock is stopped and making single-stepping and halting the CPU easier.
The CMOS variant also has a Bus Enable (BE) pin. Like similar pins on later, more advanced processors, this pin puts the address, data, and R/W pins into a high impedance state, giving other peripherals and microcontrollers the ability to write to RAM, peripherals, or anything else. It’s a handy feature to have if you’re using a microcontroller for everything except the CPU.
It’s already a great build, and since [Petri] has the skills to program this 8-bit ‘duino game, he’s sure to come up with something even better for this computer.
Oh, if you’re looking for something even cooler than a 3-chip 6502, there’s a bunch of stuff over on hackaday.io you should check out. Everything from 4-bit computers built from discrete components to dual AVR board can be found there.