It’s a well-known secret that inkjet ink is being kept at artificially high prices, which is why many opt to forego ‘genuine’ manufacturer cartridges and get third-party ones instead. Many of these third-party ones are so-called re-manufactured ones, where a third-party refills an empty OEM cartridge. This is increasingly being done due to digital rights management (DRM) reasons, with tracking chips added to each cartridge. These chip prohibit e.g. the manual refilling of empty cartridges with a syringe, but with the right tweak or attack can be bypassed, with [Jay Summet] showing off an interesting HP cartridge DRM bypass using a physical man-in-the-middle-attack.
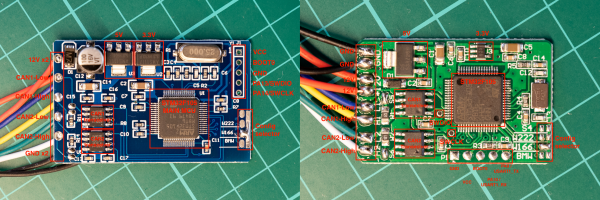
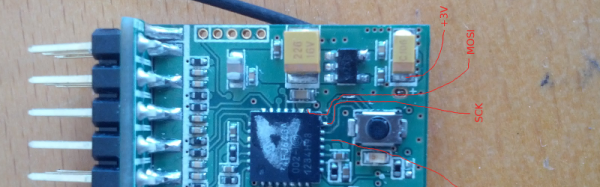
This bypass takes the form of a flex PCB with contacts on both sides which align with those on the cartridge and those of the printer. What looks like a single IC in a QFN package is located on the cartridge side, with space for it created inside an apparently milled indentation in the cartridge’s plastic. This allows is to fit flush between the cartridge and HP inkjet printer, intercepting traffic and presumably telling the printer some sweet lies so that you can go on with that print job rather than dash out to the store to get some more overpriced Genuine HP-approved cartridges.
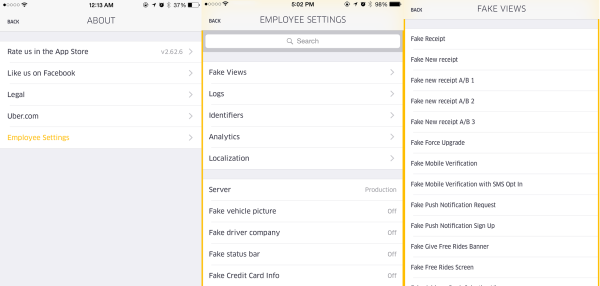
Not that HP isn’t aware or not ticked off about this, mind. Recently they threatened to brick HP printers that use third-party cartridges if detected, amidst vague handwaving about ‘hackers’ and ‘viruses’ and ‘protecting the users’ with their Dynamic Security DRM system. As the many lawsuits regarding this DRM system trickle their way through the legal system, it might be worth it to keep a monochrome laser printer standing by just in case the (HP) inkjet throws another vague error when all you want is to just print a text document.
Continue reading “Man-in-the-Middle PCB Unlocks HP Ink Cartridges”