The humble incandescent lightbulb is an invention just about anyone born in the 20th Century is more than familiar with. But it’s not the be all and end all of lighting technology – there are neon lights, compact fluorescent bulbs, and even LEDs are finally being adopted for interior lighting. But with the endless march forward, there are vintage throwbacks to the past – how many hipster cafes have you been to lately with great big industrial-looking filament bulbs hanging from the ceiling?
However, that’s not all history has to give us. These gas discharge bulbs from yesteryear are absolute works of art.
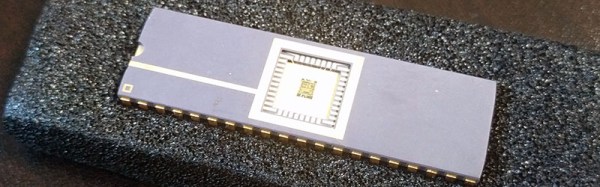
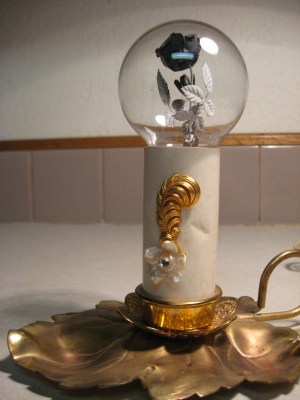
The bulbs contain delicate floral sculptures in metal, coated with phosphor, and the bulbs are filled with neon or argon gas. Applying mains voltage to the electrodes inside the bulb causes the phospor to fluoresce, creating a glowing flower that is hauntingly beautiful.
These bulbs were manufactured by the Aerolux Light Company, from the 1930s to the 1970s. Once upon a time, they could be had for as little as 20 cents a bulb – nowadays you’re likely to pay over $50 on eBay or Etsy. The bulbs work by the glow discharge effect, not at all dissimilar to garden variety neon lamps.
While it’s not easy, it is possible to make your own vacuum tubes. Maybe it’s time to order some phospor powder and a tank of neon and get to work? Be sure to document your attempt on Hackaday.io.
Thanks to [Itay Ramot] for the tip!