It sounds like something out of a sci-fi or horror movie: people suffering from complete locked-in state (CLIS) have lost all motor control, but their brains are otherwise functioning normally. This can result from spinal cord injuries or anyotrophic lateral sclerosis (ALS). Patients who are only partially locked in can often blink to signal yes or no. CLIS patients don’t even have this option. So researchers are trying to literally read their minds.
Neuroelectrical technologies, like the EEG, haven’t been successful so far, so the scientists took another tack: using near-infrared light to detect the oxygenation of blood in the forehead. The results are promising, but we’re not there yet. The system detected answers correctly during training sessions about 70% of the time, where the upper bound for random chance is around 65% — varying from trial to trial. This may not seem overwhelmingly significant, but repeating the question many times can help improve confidence in the answer, and these are people with no means of communicating with the outside world. Anything is better than nothing?
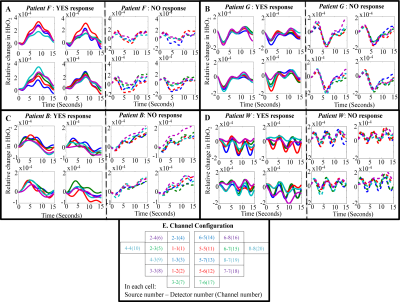 It’s noteworthy that the blood oxygen curves over time vary significantly from patient to patient, but seem roughly consistent within a single patient. Some people simply have patterns that are easier to read. You can see all the data in the paper.
It’s noteworthy that the blood oxygen curves over time vary significantly from patient to patient, but seem roughly consistent within a single patient. Some people simply have patterns that are easier to read. You can see all the data in the paper.
They go into the methodology as well, which is not straightforward either. How would you design a test for a person who you can’t even tell if they are awake, for instance? They ask complementary questions (“Paris is the capital of France”, “Berlin is the capital of Germany”, “Paris is the capital of Germany”, and “Berlin is the capital of France”) to be absolutely sure they’re getting the classifications right.
It’s interesting science, and for a good cause: improving the quality of life for people who have lost all contact with their bodies. (Most of whom answered “yes” to the statement “I am happy.” Food for thought.)
Via Science-Based Medicine, and thanks to [gippgig] for the unintentional tip! Photo from the Wyss Center, one of the research institutes involved in the study.