Pour yourself a nice hot cup of tea, because [iliasam]’s latest work on a laser rangefinder (in Russian, translated here) is a long and interesting read. The shorter version is that he got his hands on a broken laser security scanner, nearly completely reverse-engineered it, got it working again, put it on a Roomba that was able to map out his apartment, and then re-designed it to become a tripod-mounted, full-room 3D scanner. Wow.
Pour yourself a nice hot cup of tea, because [iliasam]’s latest work on a laser rangefinder (in Russian, translated here) is a long and interesting read. The shorter version is that he got his hands on a broken laser security scanner, nearly completely reverse-engineered it, got it working again, put it on a Roomba that was able to map out his apartment, and then re-designed it to become a tripod-mounted, full-room 3D scanner. Wow.
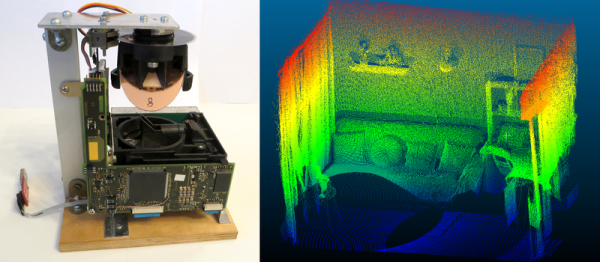
The scanner in question has a spinning mirror and a laser time-of-flight ranger, and is designed to shut down machinery when people enter a “no-go” region. As built, it returns ranges along a horizontal plane — it’s a 2D scanner. The conversion to a 3D scanner meant adding another axis, and to do this with sufficient precision required flipping the rig on its side, salvaging the fantastic bearings from a VHS machine, and driving it all with the surprisingly common A4988 stepper driver and an Arduino. A program on a PC reads in the data, and the stepper moves another 0.36 degrees. The results speak for themselves.
This isn’t [iliasam]’s first laser-rangefinder project, naturally. We’ve previously featured his homemade parallax-based ranger for use on a mobile robot, which is equally impressive. What amazes us most about these builds is the near-professional quality of the results pulled off on a shoestring budget.