If you need an industrial-strength IoT product, you need an industrial-strength WiFi chipset. For our own household hacks, we’re totally happy with the ESP8266 chip. But if you need to connect to the big, scary Internet you’ll probably want state-of-the-art encryption. In particular, Amazon insists on TLS 1.2 for their Web Services (AWS), and we don’t know how to get that working on the ESP.
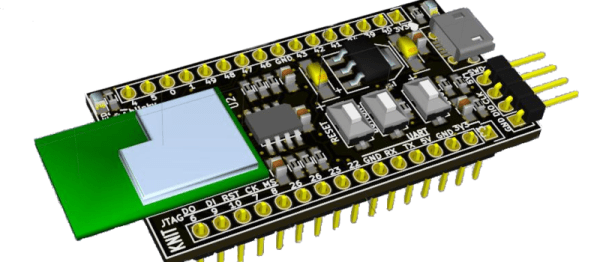
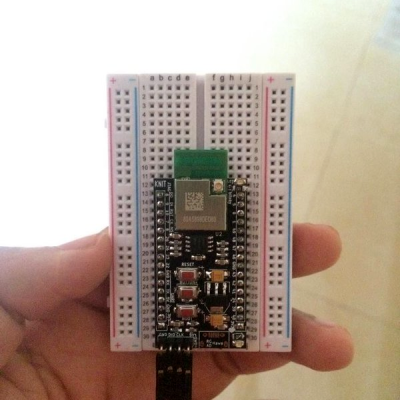
[Anuj] designed a breakout board called the knit which includes a Marvell MW300 WiFi SOC. This chip has an onboard ARM Cortex M4F running at 200 MHz, which means you’ve got a lot of everything to play with: flash memory, RAM, a floating-point unit, you name it. And Marvell’s got an SDK for using AWS that includes things like an operating system and peripheral support and other niceties. TLS 1.2 is included.
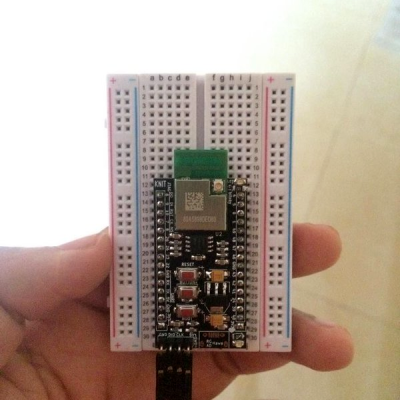 Best of all, a MW300 breakout is reasonably affordable (though more expensive than the mass-produced ESP8266 modules, naturally) and it’s an entirely open design. [Anuj] also seems to be setting up for a production run, if you don’t feel like making it yourself.
Best of all, a MW300 breakout is reasonably affordable (though more expensive than the mass-produced ESP8266 modules, naturally) and it’s an entirely open design. [Anuj] also seems to be setting up for a production run, if you don’t feel like making it yourself.
The MW300 is in all sorts of commercial IoT designs, and it’s a battle-tested go-to for interfacing with “the cloud” securely. The only hobbyist-friendly board that’s similar is the Adafruit WICED WiFi Feather, but it’s more expensive, less powerful, and out of stock at the moment, which just shows the demand for something like this.
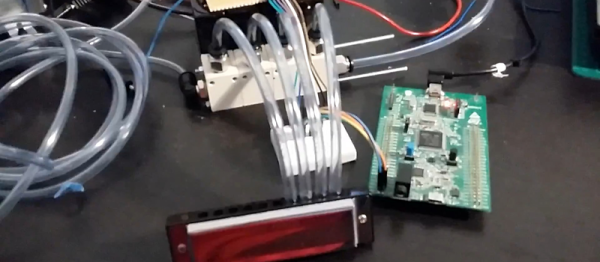
Of course, if you need more integrated peripherals, you could just hack up a “Hello Barbie” toy which has the same chip as well as sweet audio codecs and a nice fat flash ROM.
We think it’s neat that [Anuj] would make and test a breakout for this powerful little WiFi SOC. We don’t need one for our projects right now — we’re running in entirely insecure mode — but it’s good to know what your options are. (We’re also looking into esp-open-rtos for the ESP8266 — we know they’ve been working on TLS 1.2 encryption, but we don’t know what their status is at the moment. Anyone?)

 Best of all, a MW300 breakout is reasonably affordable (though more expensive than the mass-produced ESP8266 modules, naturally) and
Best of all, a MW300 breakout is reasonably affordable (though more expensive than the mass-produced ESP8266 modules, naturally) and