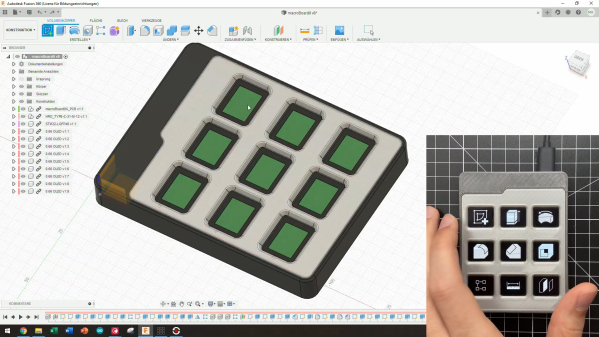
We’re used to the idea of a macropad, a small extension keyboard for your computer whose keys can be programmed to the functions of your choice. They can be made in many ways, but they all follow a similar functionality. Deepdeck from [Nick Velasquez] is another matter, an attempt to make a macropad with functionality that goes way beyond simply pressing keys.
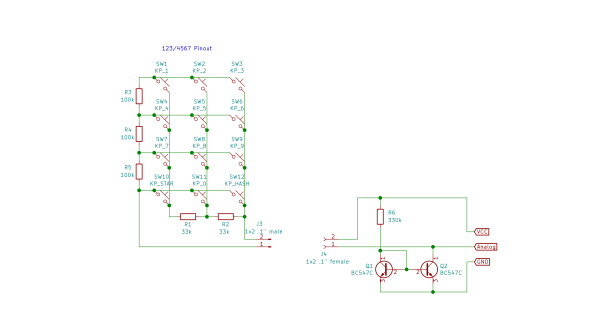
At its heart is an ESP32 module, and it makes full use of both Bluetooth and wireless networking capabilities. It can use Bluetooth when connecting to the host computer, and the wireless connection hosts both the configuration interface via a web server and an Internet connection from which it derives those special powers. This is a macropad with programmable keys just like all the others, but it also has the ability to connect to online APIs programmed by the user. This allows it to automate complex queries involving other sources into a keypress, which gives it many more possibilities.
A tool such as this one is one of those things which requires a bit of thought as to exactly how it might be used. A normal API connected device might display the weather on a screen for instance, but how often does one need to type the weather forecast? However we can see that this extra online dimension will find as yet unseen applications, and we look forward to the idea being taken up with other macropads.