Solar power has gotten cheap enough that putting up panels is among the cheapest ways of providing energy. This isn’t just the case for bulk electricity on a power grid, either; even small devices are easier and cheaper to power with solar than ever before. For example, landscape lighting which once relied on 12V or 24V DC wires all over one’s yard with a transformer and power supply hidden somewhere have partially been converted to simpler individual solar-powered lights now. These small devices can also be given additional capabilities as [Mauro] demonstrates.
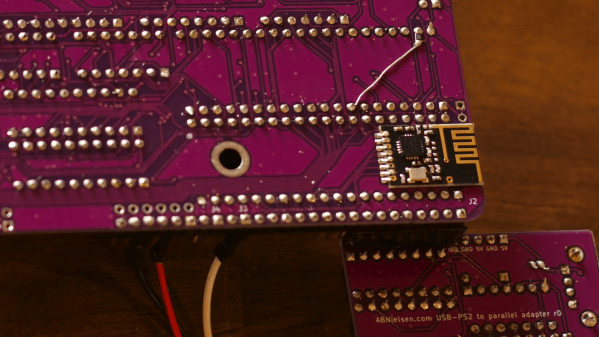
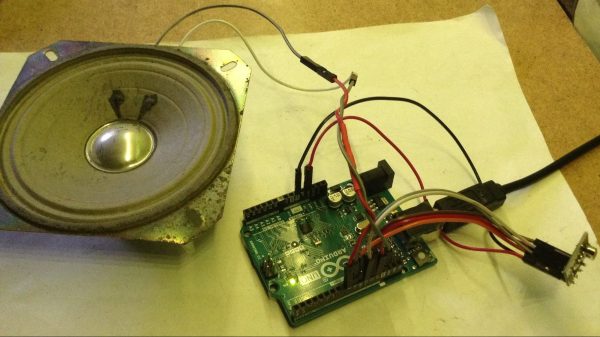
In this case, [Mauro]’s goal was to add on-demand lighting to a solar-powered light which was otherwise motion-activated only. To do this, they added a NRF24L01+ radio inside the light’s housing paired with an STM32 microcontroller. This secondary system is largely separated from the existing control circuitry with the exception of being able to switch the lights and receiving its power from the same solar panel. [Mauro] also created a small library to help with communicating with these new modules, whether that’s using a home automation system like Home Assistant or some other method.
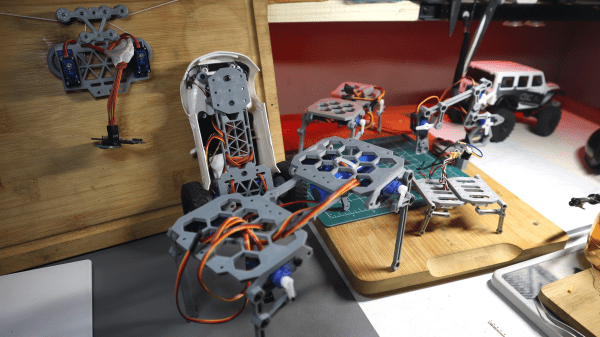
Although adding in a few capabilities to inexpensive solar lighting might seem simple on the surface, a project like this is a gateway to adding in all kinds of interesting features to things with built-in solar panels and lots of free space in their cases. The best example here is the addition of a Meshtastic node to one of these lights, making it convenient and stealthy, but we could also see adding in other remote hardware to a landscape lighting module like a gate sensor or a plant health monitoring system.


 nRF24L01 boards and build yourself a copy of the remote control [saul] handily provides in
nRF24L01 boards and build yourself a copy of the remote control [saul] handily provides in