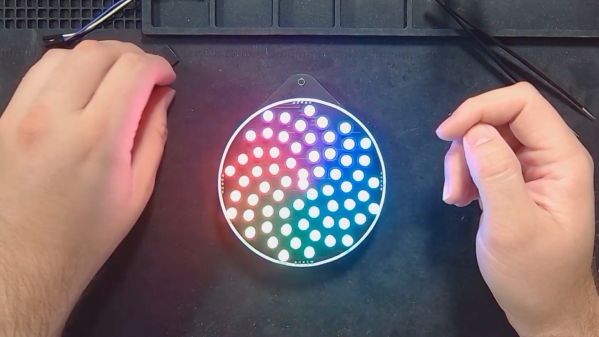
For those of us licensed in other countries it comes as something of a surprise to find that American radio amateurs now have to run RF exposure calculations as part of their licence requirements. [Ham Radio Crash Course] as approached this in a unique fashion, by running around 800 watts of 6-metre power into a vertical antenna festooned with hotdogs. That’s right, this ham is trying to cook some ‘dawgs! Is his station producing dangerous levels of power that might cook passers-by?
Of course, aside from a barely-warmed line along where the ‘dogs were attached to the antenna there’s no heating to be found. But we think he’s trying to make the point in the video below the break about the relative pointlessness of applying RF field limits which are definitely relevant at much higher frequencies, to hams at low frequencies.
It leaves us curious as to how that 800 watts could be efficiently transferred into the sausages and really cook them. Strapping them to a vertical is we think the equivalent of strapping anything resistive to a conductor, they do not form a significant enough part of the circuit. We think that even six metres could cook a sausage if it could be efficiently coupled into it, so we’d suggest putting a grounded sausage up the middle of a close-wound helix.
If you have any thoughts on the RF exposure calculations, or on the best way to cook a ‘dog with 6m, we’d love to hear the, in the comments. Meanwhile, this isn’t the first piece of ‘dog-based shenanigans we’ve brought you.