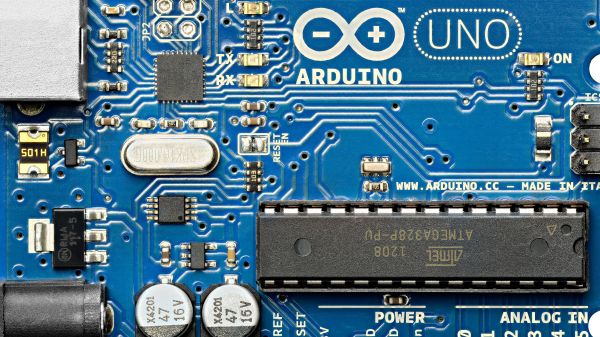
These days, most of our microcontroller boards come with bootloaders so you can squirt hex into them straight over USB. However, you don’t need to do things this way. If you’re more old school, you can program your AVRs right from a Commodore 64. [Linus Akesson] shows us how.
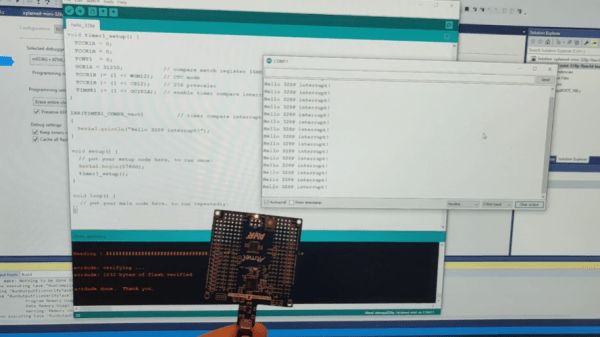
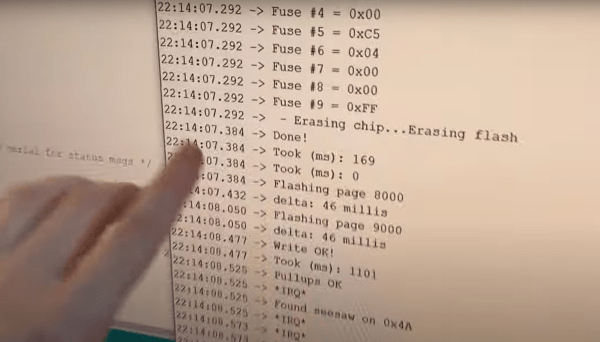
Programming an AVR isn’t that hard. By holding the chip in reset, it’s possible to flash code via a serial protocol using just three wires. However, that’s pretty impractical to do with modern PCs — they don’t come with addressable IO pins anymore. Normally, you’d use a dedicated programmer to do the job, but [Linus] found his had died on a Friday night. So he set about turning his C64 into one instead.
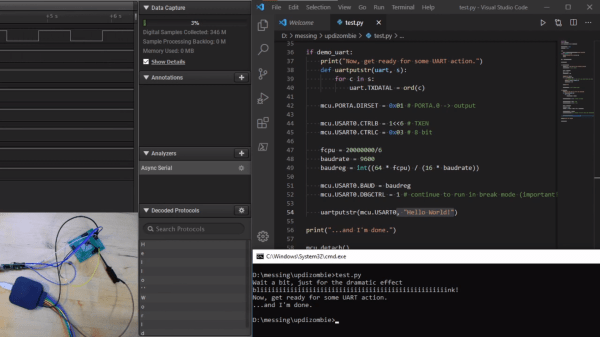
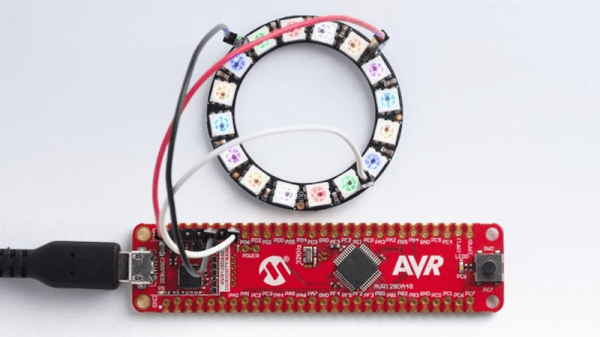
He decided to use the pins of the C64’s Joystick Port 2, with pins 1, 2, 3, and 4 hooked up to SCK, MOSI, Reset, and MISO on the AVR, respectively. 5 V and Ground were also provided courtesy of the C64’s port. He then whipped up a simple bit of assembly code to read a bit of AVR hex and spit it out over the Joystick port following the in-circuit programming protocol. With a 1541 Ultimate to load files on to the C64 in hand, it was easy to pull his compiled AVR program off his modern PC, chuck it on the C64, and then get the old Commodore to program the AVR in turn.
It’s not the first time [Linus] has wowed us with a C64 in hand. If you’ve got your own fresh projects for the best-selling computer of all time, don’t hesitate to let us know!