A healthy aquarium ecosystem requires very specific conditions, with factors like the salinity and temperature having to be just right to keep said ecosystem happy. As some species are adapted to fairly cold water, this requires the use a water chiller. Recently [The Blunt Oracle] modified one of these aquarium-focused chillers with a much better controller to make it both more accurate and potentially more efficient as well.
A healthy aquarium ecosystem requires very specific conditions, with factors like the salinity and temperature having to be just right to keep said ecosystem happy. As some species are adapted to fairly cold water, this requires the use a water chiller. Recently [The Blunt Oracle] modified one of these aquarium-focused chillers with a much better controller to make it both more accurate and potentially more efficient as well.
The target for the surgery was a generic Shanhuchong Y-160 chiller that after a brief teardown turned out to use an STC-1000 style controller. The biggest disadvantage with this unit is probably that it just has one temperature probe, which monitored the temperature of the heat exchanger rather than that of the chilled water tank.
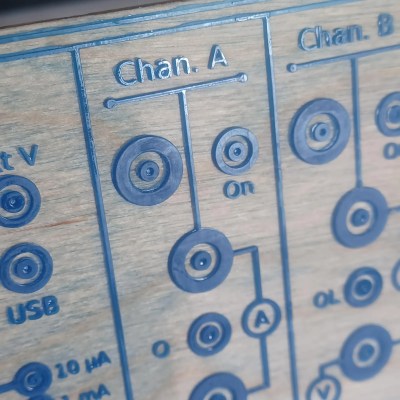
This controller was replaced with a Wi-Fi-equipped Elitech ECS-974T sourced for $50 off AliExpress that uses the same 71 x 29 mm form factor. Following that it was just a matter of some creative rewiring – as shown in the top image – and installing the twin temperature probes of the new controller.
Being able to monitor also the temperature of the chilled water adds a layer of redundancy that’s very welcome after splurging thousands of clams on a fancy aquarium and its inhabitants. As a bonus the Wi-Fi interface allows for it to be monitored and controlled remotely, with [The Blunt Oracle] pushing the Home Assistant configuration in a PR as well that recently got merged. They’d also like to extend their thanks to Elitech for having pretty good documentation that really helped with creating the HA configuration file, which is a rarity with many of such controllers.