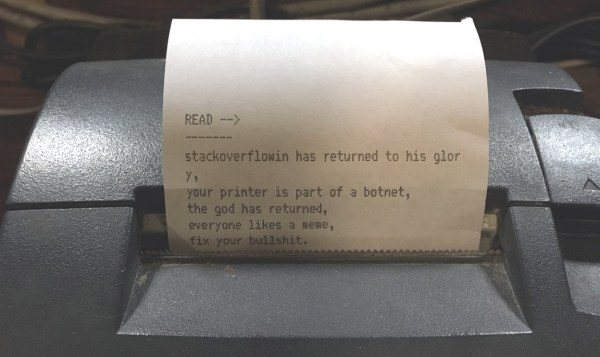
A new day dawns, and we have another story involving insecure networked devices. This time it is printers of all makes and descriptions that are causing the panic, as people are finding mystery printouts bearing messages such as this:
“Stackoverflowin has returned to his glory, your printer is part of a botnet, the god has returned“
Well that’s it then, you can’t argue with a deity, especially one who has apparently created a botnet from the world’s printing devices. Printer owners the world over are naturally worried about their unexpected arrival, and have appeared on support forums and the like to express their concern.
We are of course used to taking everything our printers tell us at face value. Low on ink? I hear you, my inanimate reprographic friend! But when our printer tells us it’s part of a botnet perhaps it’s time to have a little think. It is entirely possible that someone could assemble a botnet of compromised printers, but in this case we smell a rat. Only in farcical crime dramas do crooks announce their crimes in such a theatrical fashion, you might say it’s the point of a botnet not to be detected by its host. Reading some of the reports it seems that many of the affected systems have port 9100 open to the world, that’s the standard TCP printer port, so it seems much more likely that someone has written a little script that looks for IP addresses with port 9100 open, and trolls them with this message.
The real message here is one with which we expect Hackaday readers will be very familiar, and which we’ve covered before. Many network connected appliances have scant regard for security, and are a relative push-over for an attacker. The solution is relatively straightforward to those of a technical inclination, be aware of which services the devices is exposing, lock down services such as uPNP and close any open ports on your router. Unfortunately these steps are probably beyond many home users, whose routers remain with their default manufacturer’s settings for their entire lives. It’s a shame our printer troll didn’t add a link to basic router security tips.
If you want to have a little fun, some of the printed pages include an email address for ‘the god’. It would be fun to figure out who this is, right?






 So given a disaffection with the ubiquity of Nixies you might think that no Nixie project could rekindle that excitement. That might have been true, until the videos below the break came our way. [Tobias Bartusch] has made his own Nixie tube, and instead of numerals it contains
So given a disaffection with the ubiquity of Nixies you might think that no Nixie project could rekindle that excitement. That might have been true, until the videos below the break came our way. [Tobias Bartusch] has made his own Nixie tube, and instead of numerals it contains 








