Temperature is a delicate thing. Our bodies have acclimated to a tight comfort band, so it is no wonder that we want to measure and control it accurately. Plus, heating and cooling are expensive. Measuring a single point in a dwelling may not be enough, especially if there are multiple controlled environments like a terrarium, pet enclosure, food storage, or just the garage in case the car needs to warm up. [Tim Leland] wanted to monitor commercially available sensors in several rooms of his house to track and send alerts.
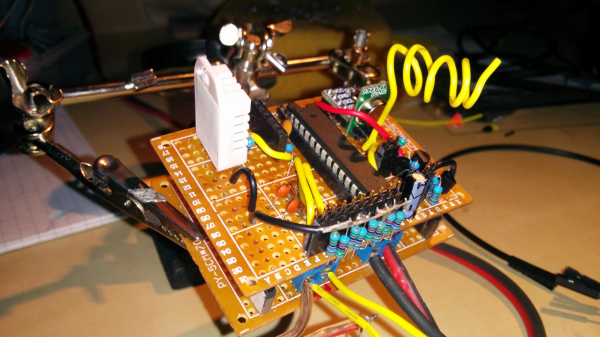
The sensors of choice in this project are weather resistant and linked in his project page. Instead of connecting them to a black box, they are linked to a Raspberry Pi so your elaborate home automation schemes can commence. [Tim] learned how to speak the thermometer’s language from [Ray] who posted about it a few years ago.
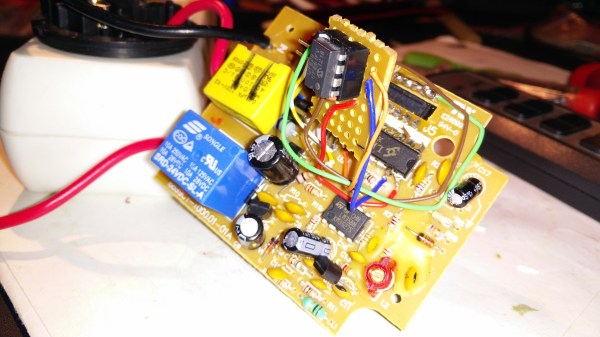
The system worked well, but range from the receiver was only 10 feet. Thanks to some suggestions from his comments section, [Tim] switched the original 433MHz receiver for a superheterodyne version. Now the sensors can be a hundred feet from the hub. The upgraded receiver is also linked on his page.
We’ve delved into thermocouple reading recently, and we’ve featured [Tim Leland] and his 433MHz radios before.