It’s that excellent time of year in which one slowly comes to the realisation that the summer’s eagerly anticipated events are now no longer at some impossibly distant point in the future, but in fact only a matter of a few months or even weeks away. For our European readers, this means that August’s SHA2017 hacker camp is appearing on the horizon, four days of outdoor technological indulgence for our community in a scout camp on the Dutch polders.
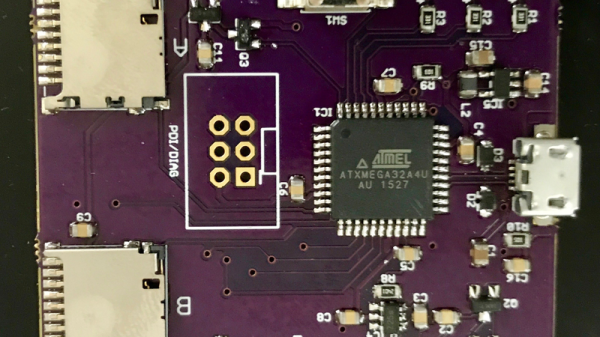
As it is a tradition of such events to have an electronic badge incorporating ever more impressive levels of computing power, it follows that the pre-production announcement of an event badge has become an important milestone in the countdown to the day. SHA2017 is no exception, and thus today we see the announcement of their take on the essentials for a hacker camp badge in 2017.
The most immediately obvious thing about the badge is its 296×128 pixel e-ink display, which should provide an immediate benefit in terms of battery life. There are the usual plethora of interfaces, GPIOs, USB, and Neopixels, and the user input is via a set of capacitive buttons. Powering the device is an ESP32, and a key design goal was to have a network for the badges that does not put pressure on the 2.4GHz infrastructure. We’re guessing they’re doing this using raw WiFi packets in the same way as the MAGfest swadge. On the software front it will provide a straightforward development route via MicroPython, and there will be an app library for those without the inclination to code their own. You can get an early look at the schematic from the project repo (PDF).
Their target is to have the badge ready and with stable software on day 1 of the event, a laudable aim if they can manage it.
Members of the Hackaday team will be making the trip to the Netherlands for SHA2017, we look forward to seeing you if you attend too, and please show us anything interesting you do with your badges! Keep your eyes peeled for the Jolly Wrench, and come say hello. You’ll find me with the OxHack contingent and giving a talk on the kit biz which I have also published in the Project to Kit series of articles.
We’ve covered so many badges here at Hackaday that we could almost serve of a retrospective exhibition of the art form. Of particular interest to us though is our own [Voja Antonic]’s badge for last year’s Hackaday SuperConference.
Thanks [Sebastius] for the tip.