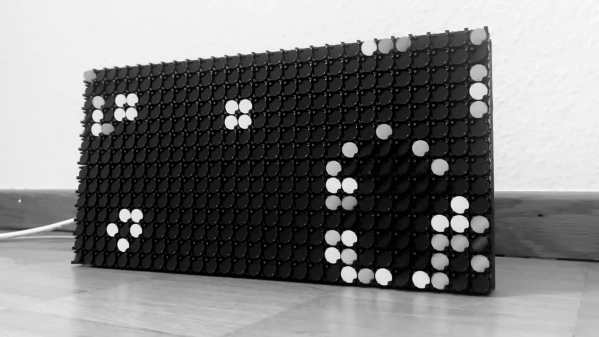
 Like many of us, [John Whittington] was saddened with the news that John Horton Conway passed away a little earlier this year, and in honor of his work, he added the Game of Life to a flip-dot display that he has been working on. The physicality of an electromechanical display seems particularly fitting for cellular automata.
Like many of us, [John Whittington] was saddened with the news that John Horton Conway passed away a little earlier this year, and in honor of his work, he added the Game of Life to a flip-dot display that he has been working on. The physicality of an electromechanical display seems particularly fitting for cellular automata.
Like what you see? If you’re curious about what makes it all tick, the display shown is an Alfa-Zeta XY5 28×14 but [John] is currently working on building them into a much larger 256 x 56 display. GitHub hosts the flip-dot simulator and driver software [John] is using, and the Game of Life functions are here.
If you’re new to the Game of Life and are not really sure what you’re looking at, [Elliot Williams] tells you all you need to know in his writeup celebrating its profound impact and lasting legacy. Watch the flip-dot display in action in the video embedded below.
Continue reading “Watch Conway’s Game Of Life Flutter Across A Flip-Dot Display”