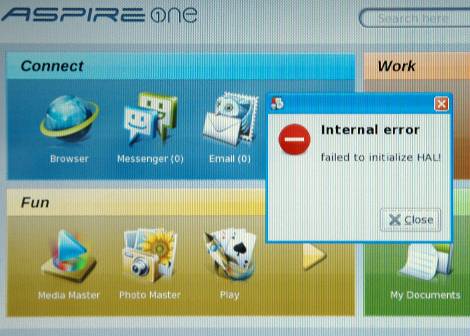
The Acer Aspire One is a netbook that often ships with a Linux OS preinstalled. This is great for fans of open source as market share is calculated based on units shipped, not what users install after they buy the hardware. Unfortunately there is a pretty major flaw that can cause a “failed to initialize HAL” error as seen above. [Michael Crummy] came up with a set of steps you can use to recover from this error.
So what is this error? HAL stands for Hardware Abstraction Layer and it’s what allows one user interface to communicate with many different types of hardware. If you’re the proud owner of an Aspire One and are struck with this error you will suddenly find that you can no longer use the USB ports, card readers, wired or wireless network connectors, or the sound card. So you can’t connect to the Internet, and you can’t get any files on or off of the device using the currently installed operating system. For an OS that [Neal Stephenson] once described as “like the M1 tanks of the U.S. Army, made of space-age materials and jammed with sophisticated technology” this is a very big problem.
We know what you’re thinking… boot into a live session on a thumb drive and get what you need from the hard disk. Well that’s all fine and dandy, but you shouldn’t ever be forced to clean install Linux to fix a problem. So check out [Michael’s] method and make sure you turn off the Acer live update server which was mostly likely the cause of the problem in the first place.