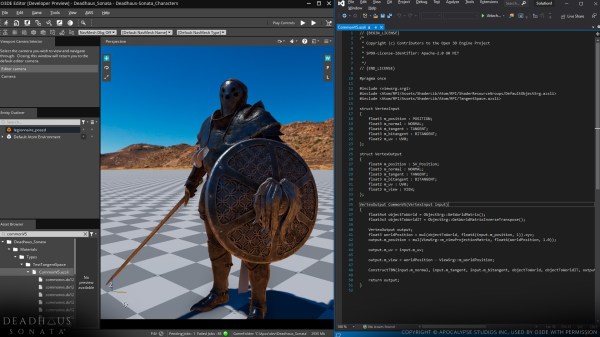
Restoring vintage technology can be a tricky business, especially without the appropriate schematics and documentation. To this end [Mark] has spent the past twelve months building a comprehensive schematic editor and circuit simulator library for electromechanical pinball machines.
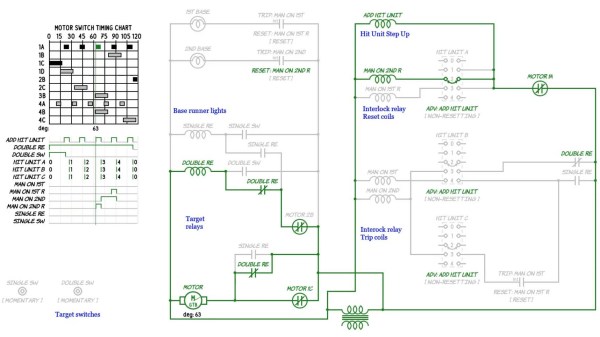
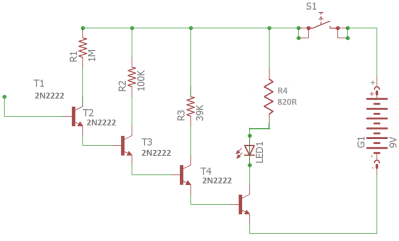
Rather than explore each and every table in excruciating detail, the emSim software aims to examine how specific circuits work, and how they are used as part of the gaming experience. The aim of the project is to aid in the diagnosis and repair of vintage electromechanical pinball machines, the types that rely on a dizzying array of switches, gears, motors and coils in their operation, operating like clockwork underneath the play field. While these older pinball machines typically use alternating current, the game logic (for the most part) is still binary, and can be effectively described with Boolean operators.
Like any machine with moving parts, these systems will eventually wear down and require servicing, a task which may not be in the wheelhouse for your casual pinball enthusiast. [Mark]’s hope is that his circuit simulations will allow just about anyone to repair these classic tables, and keep them around for future generations to explore and enjoy.
If tinkering with pinball innards isn’t for you, then make sure to check out our coverage of this awesome virtual pinball table.