The Scottish Consulate has stamped its last passport, the Dutch fire tower has belched its final flame, and the Gold Members Lounge has followed the Hacienda and the Marquee into clubland oblivion. EMF Camp 2016 is over, so all the 1500 or so attendees have left are the memories, photographs, and festival diarrhoea to remind them of their three days in the Surrey countryside.
Well, not quite all, there is the small matter of the badge.
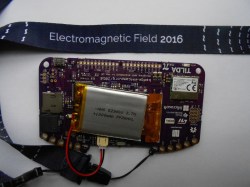
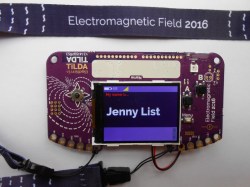
In the case of EMF 2016 it was called TiLDA MKπ, and since there was a point earlier in the year when it seemed the badge might never see the light of day it represents a significant achievement from the EMF badge team.
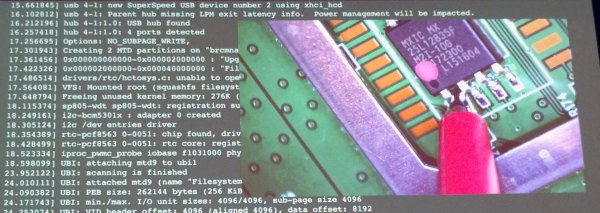
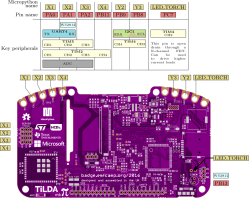
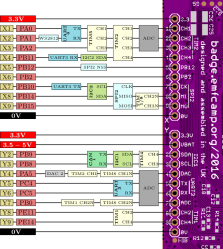
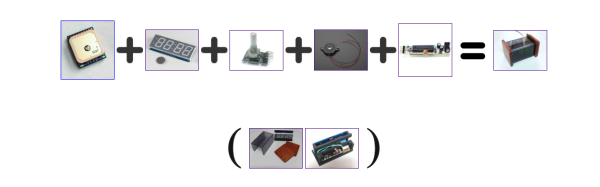
The badge features an STM32L486VGT6 ARM Cortex M4 running at 80MHz, a 320×240 pixel colour LCD, magnetometer and accelerometer, and a CC3100 WiFi processor. The firmware provides a simple interface to an app store containing an expanding array of micropython apps from both the EMF Camp team and submitted by event attendees. As shipped the badge connects to one of the site networks, but this can be adjusted to your own network after the event. It’s been designed for ease of hacking, requiring only a USB connection and mounting as a disk drive without need for special software or IDE. A comprehensive array of I/O lines are brought out to both 0.1″ pitch pins and 4mm edge-mounted holes. At the EMF Camp closing speeches there was an announcement of a competition with a range of prizes for the best hardware and software uses for the badge.
As is so often the case the badge was not without its teething troubles, as the network coped with so many devices connecting at once and the on-board Neopixel turned out to have been mounted upside down. Our badge seemed to have a bit of trouble maintaining a steady network connection and apps frequently crashed with miscellaneous Python errors, though a succession of firmware updates have resulted in a more stable experience. But these moments are part of the badge experience; this is after all an event whose attendees are likely to have the means to cope with such problems.
All the relevant files and software for the badge are fully open-source, and can be found in the EMF Camp GitHub repositories. We’ve put a set of images of the board in a gallery below if you are curious. The pinout images are courtesy of the EMF badge wiki.
We’ve featured EMF badges before, here’s our look at the EMF 2014 device.



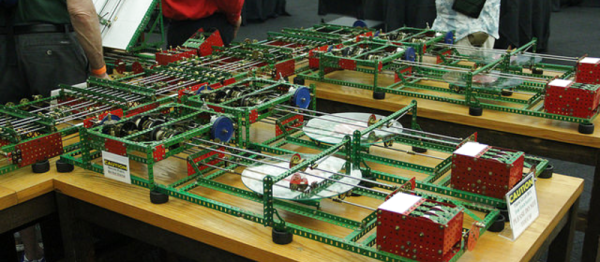
 Here at the Vintage Computer Festival, we’ve found oodles of odds and ends from the past. Some, however, have gotten a modern twist like [bitfixer’s] recent Commodore PET project upgrades.
Here at the Vintage Computer Festival, we’ve found oodles of odds and ends from the past. Some, however, have gotten a modern twist like [bitfixer’s] recent Commodore PET project upgrades.