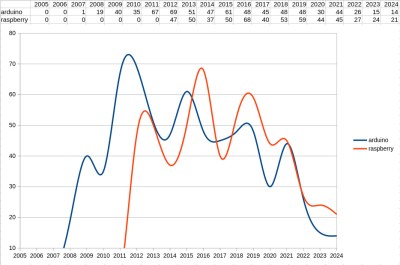
Do you remember the global chip shortage? Somehow it seems so long ago, but it’s not even really been three years yet. Somehow, I had entirely forgotten about it, until two random mentions about it popped up in short succession, and brought it all flooding back like a repressed bad dream.
Playing the role of the ghost-of-chip-shortage-past was a module for a pair of FPV goggles. There are three versions of the firmware available for download at the manufacturer’s website, and I had to figure out which I needed. I knew it wasn’t V1, because that was the buggy receiver PCB that I had just ordered the replacement for. So it was V2 or V3, but which?
Digging into it, V2 was the version that fixed the bug, and V3 was the redesign around a different microcontroller chip, because they couldn’t get the V2 one during the chip shortage.
I saw visions of desperate hackers learning new toolchains, searching for alternative parts, finding that they could get that one chip, but that there were only 20 of them left and they were selling for $30 instead of $1.30. I know a lot of you out there were designing through these tough couple years, and you’ve all probably got war stories.
And yet here we are, definitively post-chip-shortage. How can you be sure? A $30 vape pen includes a processor that we would have killed for just three years ago. The vape includes a touchscreen, just because. And it even has a Bluetooth LE chip that it’s not even using. My guess is that the hardware designers just put it in there hoping that the firmware team would get around to using it for something.
This vape has 16 MB of external SPI Flash! During the chip shortage, we couldn’t even get 4 MB SPI flash.
It’s nice to be on the other side of the chip shortage. Just order whatever parts you want and you get them, but don’t take for granted how luxurious that feels. Breathe easy, and design confidently. You can finally use that last genuine STM32F103 blue pill board without fear of it being the last one on earth.
(Featured image is not an actual photo of the author, although he does sometimes have that energy.)