After we last saw [David Lovett] of [Usagi Electric], he was knee-deep in trying to fix a DEC PDP-11/03 power supply, which fortunately led to a fixed PSU and a very happy PDP-11/23 system installed in the enclosure, as he covers in today’s video. Previously, we had covered his debugging attempt of this very much dead power supply, which had led [David] down many fruitless rabbitholes. By the time he was taking various components off the board to try and induce certain results, he threw in the towel and went back to the drawing board, assisted with many community comments.
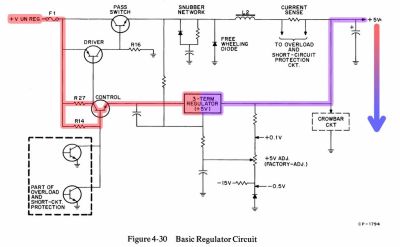
Much of the confusion came down to not really understanding how this PDP-11/03 PSU design works, which isn’t that crazy in hindsight, considering how quaint it is. Although [David] originally focused on the +5V rail, a small detail that was in the schematics is that the 5V rail is based around a 7805 that has its ground referenced to the -15V rail.
It is this 7805 that provides a linearly regulated 5V rail up till its current limit, at which point the control transistor gets biased sufficiently to start conducting, which eventually triggers the driver transistor that is responsible for driving the pass switch transistor. This then charges L2 from the unregulated supply, which is used effectively as a switching mode power supply until the current across the 7805 drops sufficiently that it becomes the primary 5V rail source again. This repeats at a kHz rate, making it more or less an SMPS as we know it today, but heavily reliant on the -15V rail as can be observed in the schematic. Continue reading “Fixing A PDP-11/03 Power Supply Is Easy When You Understand It”