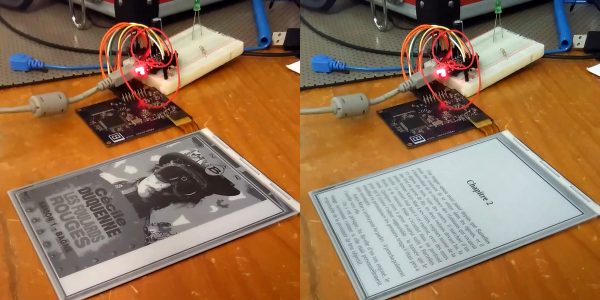
E-ink displays are awesome. Humans spent centuries reading non-backlit devices, and frankly it’s a lot easier on the eyes. But have you looked into driving one of these critters yourself? It’s a nightmare. So chapeau! to [Julien] for his FPGA-based implementation that not only uses our favorite open-source FPGA toolchain, and serves as an open reference implementation for anyone else who’s interested.
Getting just black and white on an E-ink display is relatively easy — just hit the ink pixels with the same signal over and over until they give up. Greyscale is made by applying much more nuanced voltages because the pixels are somewhat state-dependent. If the desired endpoint is a 50% grey, for instance, you’d hit it with a different pulse train if the pixel were now white versus if it were now black. (Ever notice that your e-book screen periodically does a white-black flash? It’s resetting all the pixels to a known state.) And that’s not even taking into account the hassles with the various crazy voltages that E-ink displays require, which [Julien] wisely handed off to a dedicated chip.
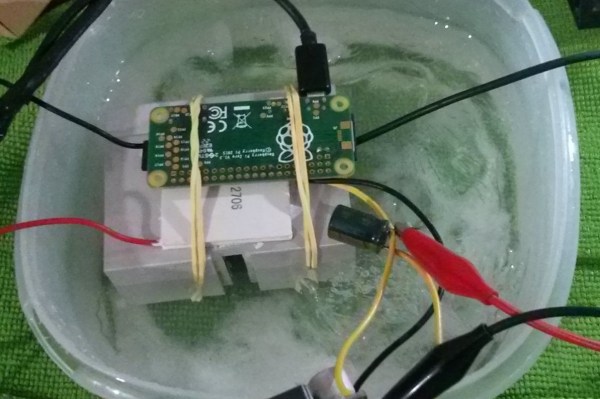
In the end, the device has to make 20-50 passes through the screen for one user-visible refresh. [Julien] found that the usual microcontrollers just weren’t capable of the speed that he wanted, hence the FPGA and custom waveform tables. We’ve seen E-ink hacks before, and [Julien] is standing on the shoulders of giants, most notably those of [Petteri Aimonen] and [Sprite_tm]. [Julien]’s hack has the fastest updates we’ve ever seen.
We still can’t wait for the day that there is a general-purpose E-ink driver chip out there for pennies, because nearly every project we make with a backlit display would look better, and chew through the batteries slower, with E-ink. In the meantime, [Julien]’s FPGA implementation is pretty close, and it’s fully open.
Continue reading “E-ink Display Driven DIY” →