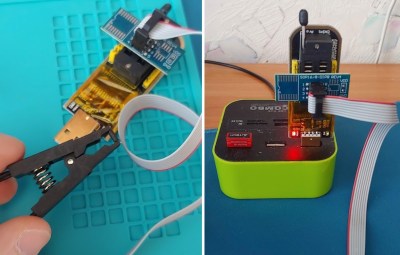
Old parts such as EPROMs will often find themselves for sale on sites such as eBay, where they are sometimes snapped up by retrocomputing enthusiasts in search of interesting code. Vintage Computer Federation forum member [GearTechWolf] picked up a clutch of IBM-labelled chips, and as int10h reports, stumbled upon a previously unknown PC-AT BIOS version which even hints at a rare PC model as yet unseen.
The IBM AT and its various versions are extremely well known in the retro PC world, so while this was quickly identified as an IBM BIOS from 1985 and narrowed down to a member of the AT family, it didn’t fit any of the known versions which shipped with the ubiquitous 1980s computer. Could it have been from an industrial or rack mount variant? It’s a possibility, but the conclusion is that it might contain a patched BIOS version of some kind.
Lacking real hardware, it happily boots on an emulator. It’s another piece of the PC historical jigsaw for people interested in computer history, and with luck in time someone will unearth an example of whatever it came from. If you find it, try a modern OS on it!