In the last two articles, I talked about two systems relying on audio notifications. The first one is the Alt-Tab annihilator system – a system making use of my window monitoring code to angrily beep at me when I’m getting distracted. The other is the crash prevention system – a small script that helps me avoid an annoying failure mode where I run out of energy before getting myself comfortable for it.
I’ve been appreciating these two systems quite a bit – not only are they at my fingertips, they’re also pretty effective. To this day, I currently use these two systems to help me stay focused as I hack on my own projects or write articles, and they are definitely a mainstay in my self-hacking arsenal.
There is a particular thing I’ve noticed – audio notifications help a fair bit in a way that phone or desktop notifications never would, and, now I have a framework to produce them – in a way that calls for a purpose-tailored device. It’s just wireless headphones, Pi-powered, connected through WiFi, and a library to produce sounds on my computer, but it turns out I can squeeze out a lot out of this simple combination.
Here’s a pocketable device I’ve developed, using off-the-shelf hardware – an audio receiver/transmitter with extra IO, paired to my laptop. And, here’s how I make use of this device’s capabilities to the fullest.
Audio Output
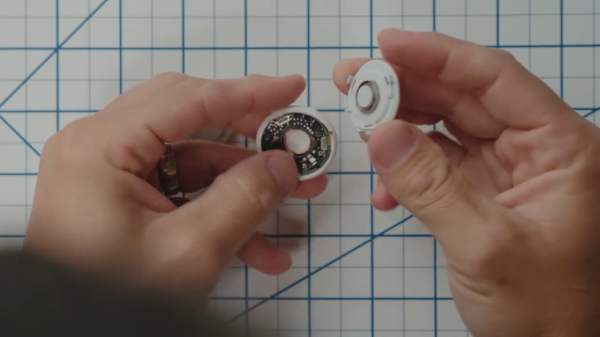
In the “producing sound out of a Pi” article, I’ve mentioned USB-C 3.5mm soundcards. You can use them with a USB-C host port, and you don’t even need any sort of resistors for that – the soundcard doesn’t try and detect state of the CC pin, and why would it, anyway? Get VBUS, GND, D+, and D-, and you got yourself an audio card with high quality output.